With better of leak websites on the forefront, this overview units the stage for an insightful dialogue on a charming subject that raises questions on safety, ethics, and accountability. From understanding what leak websites are to exploring their impression and authorized implications, we delve into the world of leaks and their penalties.
Regardless of the significance of safety, leaks proceed to pose a big threat to people and organizations. The results of such leaks may be far-reaching, affecting not solely these instantly concerned but in addition the broader group. This dialogue highlights the necessity to perceive the character of leak websites, their varieties, and the measures that may be taken to forestall them.
Varieties of Leak Websites
Leak websites are net platforms that host confidential or labeled data disclosed by these licensed to entry them. These websites have garnered important consideration for his or her capability to make clear authorities corruption, company malfeasance, and different types of abuse of energy, by offering the general public with in any other case inaccessible data. By analyzing the varied sorts of leak websites, one can higher perceive the capabilities they serve and the dangers they pose.
Mainstream Leak Websites
Mainstream leak websites are massive, well-established platforms that combination and publish leaked data from world wide. Characterised by their huge consumer base, sturdy editorial presence, and rigorous fact-checking processes, mainstream leak websites have turn into key sources of knowledge for investigative journalists and whistleblowers alike. A number of the most notable mainstream leak websites embody WikiLeaks and The Intercept.
Mainstream Leak Examples:
- WikiLeaks, based in 2006, has revealed hundreds of leaked paperwork and recordings from numerous sources, together with authorities and company archives.
- The Intercept, launched in 2014, has launched quite a few reviews based mostly on leaked data obtained from authorities and personal entities.
These platforms’ affect lies of their capability to curate and contextualize leaked data, making it extra accessible and impactful to a wider viewers.
Crypto-Centric Leak Websites
Crypto-centric leak websites function independently from conventional mainstream media and infrequently prioritize anonymity and cryptocurrency-facilitated transactions. These websites ceaselessly depend on encrypted channels and decentralized storage options to guard the identities of their sources and keep information integrity.
Crypto-Centric Leak Web site Examples:
- Riseup: An encrypted electronic mail and chat service providing nameless communication and file-sharing options, making it a gorgeous choice for these searching for safety from surveillance.
- ProtonMail: A safe emailing service that prioritizes consumer anonymity and makes use of end-to-end encryption for safe communication.
These websites cater to people who require enhanced safety measures and a sure stage of detachment, making it tougher for authorities to trace and determine customers.
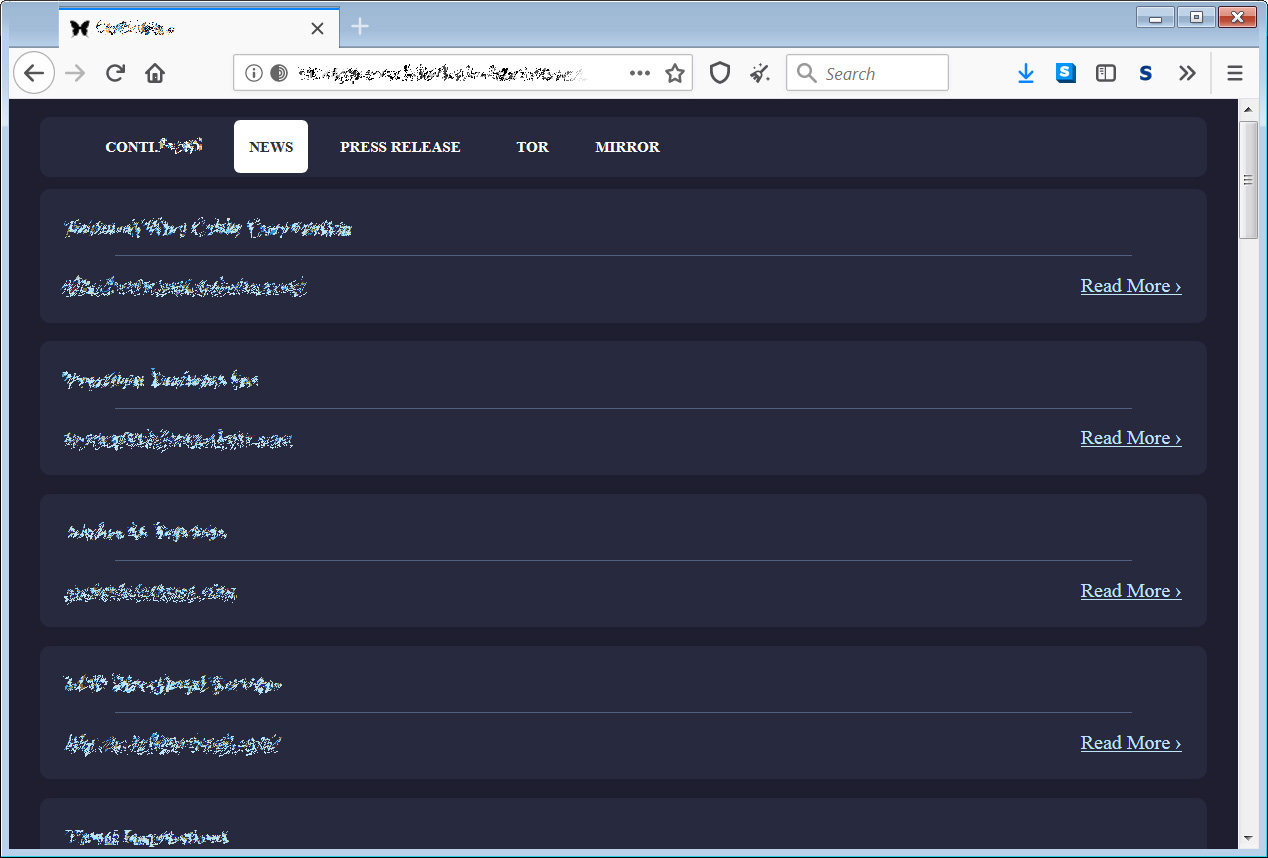
Darkish Net Leak Websites
Darkish net leak websites occupy essentially the most clandestine nook of the web, requiring particular software program to entry. These websites primarily host delicate data obtained from compromised authorities or company databases and ceaselessly comprise malware, phishing scams, or different malicious content material. Their principal viewers consists of black-hat hackers and cyber-activists.
Darkish Net Leak Web site Dangers:
- Malware and phishing scams may be transmitted by way of these websites, compromising customers’ gadgets and monetary data.
- Darkish web pages ceaselessly comprise misinformation or disinformation, which might result in confusion and undermine belief in genuine leak websites.
- Collaborating in these websites can have critical authorized penalties because of involvement in or facilitation of black-hat actions.
The dangers related to interacting with darkish net leak websites far outweigh any perceived advantages, making them usually unfavorable for legit customers.
State-Sponsored Leak Websites
State-sponsored leak websites are platforms developed and managed by governments themselves to host labeled data or leak counter-narratives. They usually purpose to govern public notion and obscure details associated to their nation’s actions.
State-Sponsored Leak Examples:
- Onion Mountain (now inaccessible), a state-sponsored platform run by Russia, launched delicate paperwork in an try to embarrass US presidential candidate Hillary Clinton.
- Hacking Group’s inside leaks, later launched through a state-linked platform, supplied perception into how governments secretly monitor and goal opponents.
These platforms’ motivations are sometimes ulterior and serve to govern public opinion or protect state actions from scrutiny, versus genuinely serving whistleblower or journalist pursuits.
Influence of Leak Websites
The proliferation of leak websites has far-reaching penalties that reverberate throughout numerous elements of society, financial system, and politics. These platforms, as soon as thought of the area of whistleblowers and investigative journalists, have now transcended their authentic function, elevating complicated questions concerning the stability between transparency and accountability.
Leaks have traditionally been used as a way to show authorities corruption, company malfeasance, and different types of malpractice, usually shedding mild on darkish secrets and techniques that had been hidden from the general public. Nonetheless, with the appearance of recent applied sciences and the rise of social media, leak websites have advanced into highly effective instruments that may both improve or undermine democratic values and establishments.
Exposing Authorities Corruption
Leak websites have been instrumental in exposing authorities corruption and misconduct, from Panama Papers to Paradise Papers. These revelations have sparked international debates on tax evasion, cash laundering, and the position of offshore monetary facilities in perpetuating inequality and corruption.
- The Panama Papers uncovered over 12 million secret paperwork revealing huge tax evasion schemes and cash laundering by politicians, enterprise leaders, and celebrities worldwide.
- Much like the Panama Papers, the Paradise Papers uncovered monetary dealings of politicians, company leaders, and rich people, highlighting the shut ties between politics and finance.
- These leaks not solely uncovered the huge networks of shell firms and tax havens but in addition raised questions concerning the lack of transparency and accountability in monetary transactions.
Threats to Nationwide Safety
The proliferation of leak websites has additionally raised considerations about nationwide safety and the potential dangers of labeled data falling into the flawed palms. Governments have responded with measures to forestall unauthorized disclosure and counter-leak methods to mitigate the impression of delicate data being leaked.
| Threats to Nationwide Safety | Classification of delicate data |
| Unauthorized disclosure | Counter-leak methods |
Challenges to Company Accountability
Leak websites have additionally highlighted the necessity for better company accountability, as firms are sometimes discovered to be partaking in questionable practices, together with environmental degradation, labor exploitation, and corruption. This has led to elevated requires better regulation and oversight of company actions.
- The leaks have uncovered the practices of huge companies, together with Amazon, Google, and Fb, on subjects starting from tax avoidance to environmental harm.
- The leaks have proven that these firms usually use complicated monetary buildings and lobbying efforts to affect authorities insurance policies and keep away from accountability.
- Leak websites have highlighted the necessity for better transparency and accountability in company dealings, as the general public calls for extra from firms when it comes to accountability and sustainability.
Surveillance and Censorship
Leak websites have additionally raised considerations about surveillance and censorship, as governments and highly effective pursuits usually search to suppress data that’s deemed threatening to their energy or management. This has led to elevated requires on-line freedom and the safety of whistleblowers.
“A leak website is simply as sturdy as its safety.” – Nameless Whistleblower
Measures to Forestall Leaks
Whereas leak websites proceed to proliferate and pose important challenges, it’s essential to give attention to measures that may forestall the dissemination of delicate data. Efficient preventive methods are important to reduce the impression of leaks and shield in opposition to potential hurt.
To fight the leak website phenomenon, authorities and organizations should undertake a multi-faceted strategy that includes technological, legislative, and cultural elements.
Tech-Based mostly Options
A number of technological options will help forestall leaks by figuring out and isolating delicate data earlier than it’s uploaded to the web. These measures embody:
- Superior Knowledge Loss Prevention (DLP) instruments: These methods can detect and forestall delicate data from leaving a company’s networks. By monitoring electronic mail, chat, and document-sharing actions, DLP instruments can flag and block probably delicate information from being shared or leaked.
- Encrypted communication platforms: Utilizing safe electronic mail providers and messaging apps with end-to-end encryption can significantly cut back the danger of delicate data being intercepted or leaked.
- Content material Administration Techniques (CMS): Implementing sturdy CMS can allow organizations to watch and management the dissemination of delicate data on their web sites and on-line platforms.
The effectiveness of those applied sciences depends closely on common software program updates, correct worker coaching, and a tradition that prioritizes information confidentiality.
Knowledge Governance and Safety Frameworks
Establishing clear information governance and safety frameworks can considerably mitigate the danger of leaks. This contains:
- Knowledge Classification: Organizations should classify delicate data based on its stage of confidentiality. This classification system allows organizations to use the required safety measures to guard delicate information.
- Entry Management: Implement stringent entry controls to make sure that solely licensed personnel can entry delicate data. This contains imposing strict password insurance policies and frequently reviewing consumer permissions.
- Common Audits and Monitoring: Conduct common safety audits and monitoring actions to determine potential vulnerabilities and forestall unauthorized entry to delicate information.
Implementing these measures requires a concerted effort from organizations and governments to prioritize information safety and confidentiality. By adopting these preventive methods, we are able to decrease the impression of leaks and cut back the danger of delicate data being compromised.
Cultural and Legislative Measures
Addressing the basis causes of leaks additionally entails addressing cultural and legislative points. This contains:
- Obligatory Knowledge Safety Legal guidelines: Enacting and imposing sturdy information safety legal guidelines can deter people and organizations from partaking in reckless information sharing practices.
- Worker Training: Educating workers on the significance of information confidentiality and the results of leaks can considerably cut back the probability of delicate data being compromised.
- Consciousness Campaigns: Organizing public consciousness campaigns concerning the dangers related to leak websites will help people perceive the potential penalties of sharing delicate data on-line.
Finally, stopping leaks requires a complete strategy that entails expertise, information governance, safety frameworks, cultural modifications, and legislative measures. By working collectively, we are able to decrease the impression of leak websites and shield delicate data from falling into the flawed palms.
Notable Instances of Leaks

The notorious leak websites have been within the limelight for a number of high-profile circumstances, showcasing the far-reaching penalties of leaked data. These situations reveal the facility of leaks in shaping public opinion, influencing coverage selections, and probably altering the course of world occasions.
From Chelsea Manning’s notorious WikiLeak dump, which revealed numerous labeled paperwork about US army operations, to Edward Snowden’s revelations concerning the NSA’s international surveillance program, the world has witnessed a number of important leak circumstances. These circumstances have sparked essential conversations about authorities secrecy, nationwide safety, and particular person freedoms.
Distinguished Hacktivist Instances
Distinguished hacktivists, usually linked to teams like Nameless, have been on the forefront of a number of high-profile leak circumstances. Some notable examples embody:
- Operation Payback (2009): A joint operation between Nameless and different hacktivists focused a number of organizations, together with the Church of Scientology and the RIAA, following the arrest of WikiLeak’s Julian Assange.
- Operation Tunisia (2010): Nameless hacked into Tunisian authorities web sites and compromised delicate data in response to the nation’s authoritarian regime.
- Operation Syria (2012): Hacktivists focused Syrian authorities web sites and uncovered delicate data, highlighting the regime’s human rights abuses.
Excessive-Profile Leaks and Their Penalties, Better of leak websites
A number of high-profile leaks have had far-reaching penalties lately, reworking the world of politics, finance, and worldwide relations.
- Chelsea Manning’s WikiLeak Dump (2010): The discharge of over 750,000 labeled paperwork revealed widespread human rights abuses, together with the killing of civilians and cover-ups by the US army.
- Edward Snowden’s NSA Revelations (2013): The previous NSA contractor uncovered the company’s international surveillance program, revealing widespread spying on world leaders, together with German Chancellor Angela Merkel.
- The Panama Papers (2016): A world collaboration of journalists and hackers unveiled a large leak of monetary paperwork, exposing widespread tax evasion and cash laundering.
Implications for World Politics
The far-reaching penalties of those leak circumstances can’t be overstated. In an period of accelerating international interconnectedness, the potential for leaks to form public opinion and affect coverage selections has by no means been increased.
The Way forward for Leaks within the Digital Age
In mild of current occasions, it’s clear that the digital age has empowered people and teams to wield important affect by way of leaks. Nonetheless, the query stays: will governments and establishments adapt to this new actuality, or will they proceed to push the boundaries of secrecy and surveillance?
Leaky, encrypted, and secretive – these attributes of recent digital life have ceaselessly altered the material of world politics. Will probably be intriguing to witness the long run growth of this area – although, that may be a matter of time.
Authorized and Moral Concerns: Finest Of Leak Websites
Leak websites usually function in a grey space, elevating complicated questions on their authorized standing and the ethics surrounding their actions. Whereas some may view these platforms as facilitators of transparency, others see them as hubs for the dissemination of delicate and labeled data. As such, the dialogue surrounding leak websites ceaselessly touches on the intersection of legislation and ethics.
Cybercrimes and the Legislation
Many people concerned in leaking labeled data through these websites threat dealing with prosecution. The Pc Fraud and Abuse Act (CFAA) in america makes it a criminal offense to interact in unauthorized entry or use of computer systems and pc methods. This legislation usually comes into play when contemplating circumstances involving leak websites.
- The CFAA can criminalize unauthorized entry to pc methods, even when no monetary hurt or different tangible penalties end result. This might lengthen to actions by people concerned in leak websites.
- Some argue that the CFAA’s broad interpretation may be seen as an try to stifle whistleblowing and free speech.
Freedom of Speech and Expression
One other pivotal moral consideration is the safety of freedom of speech and expression in relation to leak websites. These platforms usually depend on the First Modification (the U.S. invoice of rights modification defending free speech) for justification, suggesting they’re an indispensable means of unveiling truths that may in any other case stay hidden or hid.
- Many argue that leak websites are a type of journalism, exercising press freedom. Nonetheless, since they don’t adhere to standard journalistic requirements and practices, they pose a problem to current authorized frameworks.
- The moral implications of leaking delicate data with out due accountability are multifaceted. These might increase legit considerations about defending particular person rights to privateness and the safety of governments and organizations.
Judicial and Legislative Responses
The interaction between leak websites and the authorized panorama has prompted important judicial and legislative scrutiny. In america, numerous federal legal guidelines and courtroom selections have aimed to curb or regulate these platforms. Notably, a current courtroom ruling made clear that these related to leak websites might face critical penalties, even for these appearing past nationwide borders.
- The U.S. Division of Justice’s stance is that leak websites, corresponding to WikiLeaks or different like-minded operations, may be focused for prosecution no matter the place the leak originated from.
- The legislative department has been working to go the ‘Cease the Importation and Redistribution of Pirated Digital Media Act’ or the “Six Strikes” legislation, which has seen important criticism prior to now for its broad and invasive implications on web customers, particularly concerning leak websites.
Finest Practices for Customers of Leak Websites
In recent times, the rise of leak websites has created a brand new actuality for customers, researchers, and organizations alike. Because the boundaries of on-line anonymity are continually pushed, customers should pay attention to one of the best practices when navigating these platforms. This part goals to supply steerage on methods to use leak websites responsibly and successfully.
One of many main considerations for customers of leak websites is the safety of their private information. When interacting with leak websites, it is important to prioritize anonymity and safety. This implies utilizing safe connections, corresponding to Tor or VPNs, to masks your IP deal with and placement. It is also essential to keep away from utilizing private gadgets or accounts when accessing leak websites, as this will compromise your on-line id.
Authentication and Verification
In an effort to make sure the credibility and authenticity of leak websites, customers have to be cautious when verifying the authenticity of the info shared on these platforms. This entails researching the fame of leak websites, checking for critiques and rankings from different customers, and cross-verifying data with different dependable sources.
One option to confirm the authenticity of leak websites is by analyzing their observe document. Search for websites which have constantly produced high-quality and correct leaks, which have been subsequently confirmed by official sources. It is also important to concentrate on the purple flags, corresponding to websites that ask for private data or provide rewards in alternate for leaks.
Info Analysis and Contextualization
When analyzing leaks, customers should take into account a number of components, together with the context wherein the knowledge was launched and the potential biases of the people or organizations concerned. This entails critically evaluating the knowledge offered and contemplating various views earlier than coming to a conclusion.
One strategy to contextualizing leaks is by analyzing the broader social, financial, and political context wherein they befell. This will help customers perceive the motivations behind the leak and the implications it has on the bigger group. It is also important to concentrate on potential propaganda or disinformation efforts, which can be utilized to govern public opinion or obscure details.
Accountable Use and Disclosure
Customers of leak websites have a accountability to make use of the knowledge responsibly and to reveal their sources when attainable. This entails being clear concerning the origins of the knowledge and avoiding hypothesis or unsubstantiated claims.
One option to reveal accountable use is by acknowledging the efforts of whistleblowers and leakers, who usually threat their careers and fame to carry essential data to mild. It is also important to acknowledge the potential penalties of irresponsible disclosure, such because the compromise of sources or the unfold of misinformation.
Evolution of Leak Websites: Future Developments

Leak websites have turn into a big risk to international safety, with the growing frequency and complexity of information breaches. As expertise continues to advance, it’s possible that hacktivists and cyber attackers will develop new instruments and strategies to take advantage of vulnerabilities and acquire unauthorized entry to delicate data. This part will discover the anticipated developments in leak websites, together with the emergence of recent ways, applied sciences, and actors.
New Applied sciences and Instruments
————————-
The way forward for leak websites shall be formed by the event of recent applied sciences and instruments, together with Synthetic Intelligence (AI) and Machine Studying (ML) algorithms, which is able to allow superior risk actors to investigate and exploit complicated methods extra successfully. Moreover, the growing use of the darkish net and encrypted communication channels will make it simpler for hacktivists to share and purchase delicate data.
- The usage of AI-powered instruments will allow hacktivists to determine and exploit particular vulnerabilities in complicated methods extra effectively.
- The emergence of ML algorithms will permit for extra subtle social engineering assaults, making it tougher to detect and forestall.
- The darkish net and encrypted communication channels will facilitate the alternate of delicate data between hacktivists, making it tougher to trace and disrupt their actions.
New Actors and Alliances
————————-
The way forward for leak websites will even be influenced by new actors and alliances, together with nation-state sponsored teams and arranged crime syndicates. These actors will carry new ranges of sophistication and sources to the desk, additional growing the complexity and risk posed by leak websites.
- Nation-state sponsored teams will proceed to play a big position within the growth and use of leak websites, significantly of their efforts to collect intelligence and disrupt the actions of rival nations.
- Organized crime syndicates will more and more use leak websites to acquire delicate details about people and organizations, which can be utilized for extortion and different malicious functions.
- The emergence of recent actors and alliances will result in the creation of extra complicated and complicated risk profiles, making it tougher to detect and forestall leaks.
Elevated Use of Encryption and Anonymity
—————————————–
The way forward for leak websites will even be characterised by the growing use of encryption and anonymity instruments, corresponding to Tor and VPNs. These instruments will allow hacktivists to hide their identities and places, making it tougher to trace and disrupt their actions.
The Rise of Encrypted Communication Channels
Encrypted communication channels, corresponding to Sign and WhatsApp, will turn into more and more common amongst hacktivists, permitting them to speak safely and securely. This can allow them to coordinate their actions and share delicate data with out being detected.
The usage of encrypted communication channels will turn into the norm amongst hacktivists, making it tougher to trace and disrupt their actions.
The Emergence of New Darkish Net Marketplaces
The darkish net will proceed to be a hub for the alternate of delicate data, with new marketplaces rising to cater to the rising demand for stolen information. These marketplaces will provide a spread of providers, together with information brokerage, hacking instruments, and id theft.
The darkish net will proceed to be a hotbed of illicit exercise, with new marketplaces rising to cater to the rising demand for stolen information.
Ending Remarks
In conclusion, the world of leaks is complicated and multifaceted. Better of leak websites is greater than only a subject – it is a name to motion, a reminder of the significance of accountable actions and the necessity for accountability. As we transfer ahead, it’s important to undertake greatest practices for customers and to contemplate the long run developments in leak websites.
FAQs
Q: What are leak websites, and the way do they work?
A: Leak websites are on-line platforms that publish delicate or confidential data, usually compromising safety and confidentiality. They will function anonymously or pseudonymously, making them difficult to trace and shut down.
Q: What sorts of leak websites exist, and what do they share?
A: There are numerous sorts of leak websites, every sharing various kinds of delicate data. Some share private information, whereas others publish confidential enterprise data, labeled authorities paperwork, or delicate monetary information.
Q: How do leak websites impression people and organizations?
A: The results of leaks may be extreme, resulting in id theft, monetary loss, reputational harm, and even bodily hurt. For organizations, leaks can compromise enterprise continuity, have an effect on market share, and hurt worker belief.
Q: What measures may be taken to forestall leaks?
A: Stopping leaks requires a multi-layered strategy, together with sturdy information encryption, safe authentication and authorization, common safety audits, worker training on information dealing with and safety protocols, and implementing incident response plans.
Q: What are some notable circumstances of leaks?
A: There have been many notable circumstances of leaks lately, together with the WikiLeaks launch of labeled US authorities paperwork, the Panama Papers, and the Equifax information breach. Every of those incidents highlights the dangers and penalties of leaks.