IT Asset Administration Finest Practices units the stage for this complete information, providing readers an in depth overview of the significance of efficient IT asset administration in organizations. It supplies a transparent understanding of the advantages, challenges, and greatest practices related to IT asset administration, from stock administration to value administration and threat mitigation.
This text will discover the important thing elements of IT asset administration, together with stock administration, asset lifecycle administration, value administration, threat administration, compliance and regulatory necessities, staffing and coaching, know-how and instruments, change administration, and steady enchancment. By the top of this information, readers can have a stable understanding of learn how to implement efficient IT asset administration greatest practices in their very own organizations.
IT Asset Administration: Why It Issues for Your Group
Efficient IT asset administration isn’t just a greatest apply, it is a necessity for any group that desires to optimize its assets, scale back prices, and enhance effectivity. IT property, together with {hardware}, software program, and providers, are the spine of contemporary companies. Nonetheless, managing these property will be difficult, particularly for big organizations with advanced IT infrastructures.
The Function of IT Asset Administration
IT asset administration is the apply of monitoring, managing, and optimizing a company’s IT property all through their lifecycle. Its goal is to make sure that IT property are utilized effectively, successfully, and securely. This consists of figuring out, classifying, and cataloging IT property, monitoring their utilization and efficiency, and performing common upkeep and upgrades.
- Figuring out IT Belongings: This entails detecting and recording all IT property throughout the group, together with {hardware}, software program, and providers.
- Classifying IT Belongings: IT property are labeled based mostly on their sort, location, and utilization. This helps to establish which property are important, and which will be upgraded or changed.
- Monitoring IT Belongings: This entails monitoring the utilization and efficiency of IT property, and performing common upkeep and upgrades.
- Optimizing IT Belongings: This entails guaranteeing that IT property are utilized effectively and successfully, and that assets are allotted accordingly.
- Disposing of IT Belongings: This entails guaranteeing that IT property are correctly disposed of once they attain the top of their lifecycle.
Advantages of IT Asset Administration
Implementing IT asset administration greatest practices can deliver quite a few advantages to a company, together with:
Price Financial savings
By figuring out and classifying IT property, organizations can scale back prices related to redundant or out of date property. IT asset administration additionally helps to forestall over-provisioning, which may result in vital value financial savings.
Improved Effectivity
IT asset administration helps to make sure that IT property are utilized effectively and successfully, lowering the chance of downtime and bettering general system efficiency.
Enhanced Safety
IT asset administration helps to establish and observe IT property, lowering the chance of safety breaches and information theft.
Examples of Profitable IT Asset Administration Implementations
A number of organizations have efficiently applied IT asset administration greatest practices, together with:
Instance 1: XYZ Company
XYZ Company, a number one monetary providers supplier, applied IT asset administration to scale back prices and enhance effectivity. They recognized and labeled all IT property, and established an everyday upkeep schedule to make sure optimum efficiency.
Instance 2: ABC Inc.
ABC Inc., a number one know-how agency, applied IT asset administration to enhance safety and scale back prices. They established a complete IT asset administration program, which included stock administration, monitoring, and disposal of property.
Case Research of Organizations That Have Achieved Important Outcomes Via Efficient IT Asset Administration
A number of organizations have achieved vital outcomes by way of efficient IT asset administration, together with:
Case Examine 1: XYZ Company
XYZ Company achieved vital value financial savings by implementing IT asset administration. They diminished prices related to redundant or out of date property, and prevented over-provisioning.
Case Examine 2: ABC Inc.
ABC Inc. achieved vital enhancements in effectivity by implementing IT asset administration. They diminished downtime and improved general system efficiency.
Stock Administration: It Asset Administration Finest Practices

Stock administration is an important facet of IT asset administration, because it allows organizations to keep up an correct and up-to-date report of their IT property. That is important for monitoring asset lifecycles, figuring out areas for value financial savings, and guaranteeing compliance with regulatory necessities.
There are three major strategies used for stock administration: guide, automated, and hybrid approaches.
Strategies of Stock Administration
Handbook stock administration entails counting on guide processes, similar to spreadsheets or paper-based information, to trace IT property. Whereas this method is cheap, it’s usually time-consuming and liable to errors.
Automated stock administration, however, makes use of specialised software program to trace IT property. This method supplies real-time monitoring, automated asset discovery, and superior reporting capabilities. Nonetheless, it may be costly and requires vital IT assets.
Hybrid stock administration combines the advantages of each guide and automatic approaches. This technique entails utilizing a mixture of guide and automatic methods to trace IT property, which will be less expensive and simpler to handle than a totally automated system.
Examples of Stock Administration Instruments and Software program
Some fashionable stock administration instruments and software program embrace:
-
Spreadsheets similar to Microsoft Excel or Google Sheets
can be utilized to create customized stock templates and observe IT property.
-
Asset administration programs similar to ServiceNow or BMC Helix
supply superior stock administration capabilities, together with automated asset discovery and real-time monitoring.
-
Free and open-source options similar to OpenAsset
present an economical different to business stock administration software program.
Conducting Common Stock Audits
Common stock audits are important for guaranteeing information accuracy and figuring out potential points with IT property. This entails frequently reviewing stock information, verifying asset portions and places, and conducting bodily inventories to make sure that all IT property are accounted for.
To make sure the accuracy of stock information, organizations ought to take into account the next greatest practices:
- Often overview and replace stock information to mirror modifications in asset portions or places.
- Confirm asset portions and places by way of bodily inventories and audits.
- Use automated asset discovery instruments to establish new IT property and guarantee they’re correctly tracked.
- Often clear up and proper stock information to forestall information accuracy points.
Asset Lifecycle Administration
IT Asset Administration entails varied phases, every with its personal set of challenges and alternatives. Understanding these phases is essential for making knowledgeable selections about IT property, from procurement to disposal.
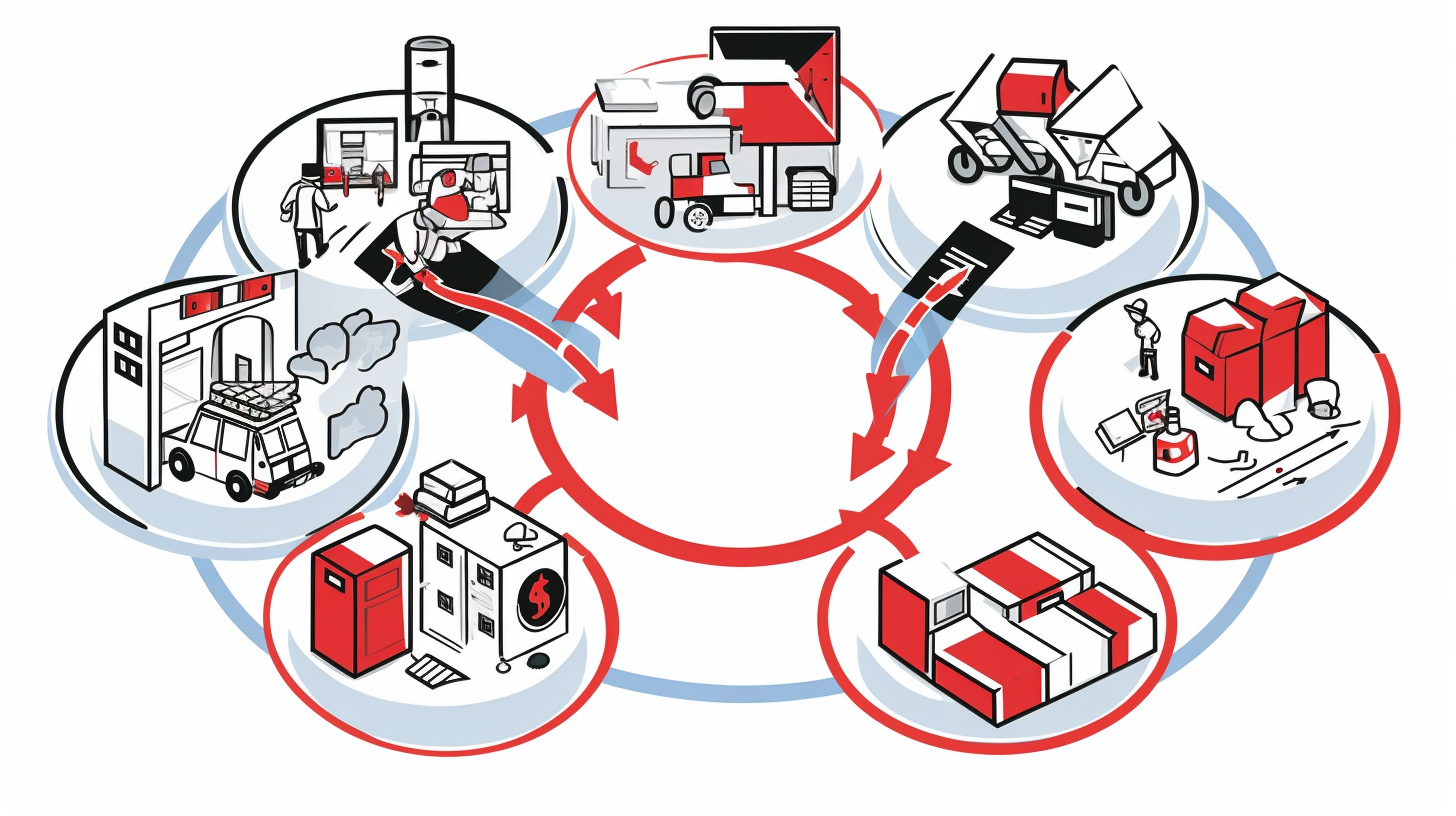
The IT Asset Lifecycle usually consists of 5 phases: Acquisition, Deployment, Upkeep, and Disposal. Every stage has a major affect on the general value, effectivity, and effectiveness of IT operations. Monitoring prices and utilization all through the lifecycle is important for making data-driven selections and figuring out areas for enchancment.
Acquisition
Acquisition is the preliminary stage of the IT Asset Lifecycle, the place organizations procure new IT property, similar to {hardware}, software program, or providers. This stage entails evaluating the wants of the group, figuring out potential distributors, and negotiating contracts. Efficient acquisition requires cautious planning, analysis, and evaluation to make sure that the acquired property meet the group’s necessities and price range.
- Outline enterprise wants and necessities
- Analysis and consider potential distributors
- Negotiate contracts and agreements
- Implement acquisition course of and procedures
Deployment
Deployment is the stage the place acquired IT property are put in, configured, and deployed to the end-users. This stage entails guaranteeing that the property are correctly built-in with present infrastructure, and that customers are adequately educated to make the most of them successfully. Environment friendly deployment requires cautious planning, testing, and validation to reduce downtime and guarantee easy operation.
- Develop deployment plans and schedules
- Conduct thorough testing and validation
- Implement deployment procedures and protocols
- Migrate information and purposes to new property
Upkeep
Upkeep is the continuing stage of the IT Asset Lifecycle, the place organizations make sure that IT property proceed to function effectively and successfully. This stage entails monitoring asset efficiency, performing common updates and patches, and addressing any points or errors that come up. Efficient upkeep requires a proactive method, with scheduled check-ups and common assessments to establish potential issues earlier than they happen.
- Develop upkeep schedules and plans
- Carry out common updates and patches
- Conduct asset well being checks and assessments
- Deal with points and errors promptly and effectively
Disposal
Disposal is the ultimate stage of the IT Asset Lifecycle, the place organizations take away or recycle IT property which are not wanted or have reached the top of their helpful life. This stage entails guaranteeing that property are disposed of in an environmentally accountable method, and that any delicate information is correctly securely erased or destroyed. Efficient disposal requires cautious planning, coordination, and execution to reduce waste and guarantee compliance with regulatory necessities.
- Develop disposal plans and procedures
- Determine and classify property for disposal
- Securely erase or destroy delicate information
- Recycle or eliminate property in an environmentally accountable method
Asset Lifecycle Administration Fashions and Frameworks
There are a number of asset lifecycle administration fashions and frameworks that organizations can use to information their IT asset administration efforts. Some fashionable fashions embrace:
| Mannequin/Framework | Description |
|---|---|
| ITIL (Data Expertise Infrastructure Library) | A service administration framework that gives steerage on IT service administration processes, together with IT asset administration. |
| COBIT (Management Goals for Data and Associated Expertise) | A framework for IT governance and administration that features IT asset administration processes and tips. |
| ISO 19770 (IT Asset Administration) | A global customary that gives tips for IT asset administration, together with information administration and software program compliance. |
Finest Practices for Extending the Lifetime of IT Belongings and Lowering Waste
Organizations can lengthen the lifetime of IT property and scale back waste by following greatest practices similar to:
- Implementing common upkeep and maintenance schedules
- Conducting thorough testing and validation earlier than deployment
- Utilizing asset utilization metrics to optimize asset deployment
- Creating and implementing sustainable IT asset disposal insurance policies
Common upkeep and maintenance might help lengthen the lifetime of IT property by 20-30%.
Price Administration
Price administration is a important element of IT asset administration, because it allows organizations to precisely observe and handle the prices related to their IT property. By doing so, corporations could make knowledgeable selections about their IT spending and optimize their budgets.
Correct Price Monitoring
Correct value monitoring is important for efficient value administration. This entails monitoring the prices of {hardware}, software program, providers, and different IT-related bills all through the asset’s lifecycle. Common audits and common opinions might help establish areas the place prices will be diminished or optimized.
Price monitoring will be carried out manually or by way of using automated instruments.
- Handbook value monitoring entails utilizing spreadsheets or different instruments to trace bills and stock.
- Automated value monitoring entails utilizing specialised software program or platforms to trace and handle prices.
Price Allocation and Price Avoidance
Price allocation and value avoidance are key methods for optimizing IT prices. Price allocation entails assigning prices to particular departments or enterprise models, whereas value avoidance entails discovering methods to scale back or get rid of pointless prices.
Price avoidance will be achieved by way of methods similar to renegotiating contracts, lowering utilization, or implementing energy-efficient applied sciences.
| Price Allocation Methods | Price Avoidance Methods |
|---|---|
| Assigning prices to particular departments or enterprise models | Renegotiating contracts with distributors |
| Utilizing value codes and classes | Lowering utilization of pointless assets |
| Monitoring prices by location | Implementing energy-efficient applied sciences |
Price Optimization Methods
Price optimization methods contain discovering methods to scale back prices with out compromising the standard or performance of IT property. Leasing and renting gear can present value advantages, as can refurbished or used gear.
Price optimization is an ongoing course of that requires common overview and evaluation of IT prices.
- Leasing or renting gear can present value advantages by way of diminished upfront prices.
- Refurbished or used gear can present vital value financial savings.
- Sustaining up-to-date stock and monitoring prices might help establish areas for discount.
Monetary Reporting and Price range Requests
Monetary reporting and price range requests are important elements of value administration. Organisations ought to put together common monetary studies, together with earnings statements, steadiness sheets, and money circulation statements.
These studies present helpful insights into IT prices and assist inform price range requests.
- Present clear and correct monetary studies to stakeholders.
- Keep detailed information of IT bills and property.
- Analyze and report on IT prices to establish areas for enchancment.
Threat Administration
Threat administration is an important facet of IT asset administration, because it entails figuring out, assessing, and mitigating potential dangers that would affect a company’s IT property. Efficient threat administration helps to make sure the safety, reliability, and integrity of IT property, which is important for sustaining enterprise continuity and supporting strategic objectives.
Potential Dangers Related to IT Belongings
IT property are weak to varied dangers, together with safety breaches, information loss, and environmental hazards. Safety breaches can happen by way of unauthorized entry, malware, or phishing assaults, which may compromise delicate information and disrupt enterprise operations. Information loss can happen as a result of {hardware} failure, software program corruption, or human error, leading to vital monetary and reputational losses. Environmental hazards similar to pure disasters, energy outages, or gear failures may also affect IT property, inflicting downtime, information loss, and reputational injury.
- Safety Breaches
The rising variety of cyberattacks and information breaches highlights the necessity for strong safety measures to guard IT property. In accordance with a report by Cybersecurity Ventures, the worldwide value of cybercrime is anticipated to succeed in $10.5 trillion by 2025. Efficient threat administration entails implementing safety measures similar to firewalls, intrusion detection programs, and encryption to forestall unauthorized entry to IT property.
Significance of Figuring out and Mitigating Dangers
Figuring out and mitigating dangers by way of efficient IT asset administration is important to reduce the affect of potential threats and guarantee enterprise continuity. By understanding the potential dangers related to IT property, organizations can take proactive measures to forestall or mitigate them. This consists of common threat assessments, asset monitoring, and vulnerability administration to establish and tackle potential safety threats.
- Threat Registers
A threat register is a software used to establish, assess, and prioritize dangers. It supplies a centralized repository of threat info, enabling organizations to trace and handle dangers successfully. In accordance with the ISO 31000 threat administration customary, a threat register ought to embrace info on threat likelihood, affect, and threat mitigation methods.
Finest Practices for Threat Administration
Conducting common threat assessments and implementing threat mitigation methods are important greatest practices for efficient threat administration. This entails staying up-to-date with the most recent safety threats, implementing strong safety measures, and frequently reviewing and updating threat administration insurance policies. Moreover, organizations ought to spend money on coaching and consciousness applications to teach staff on threat administration and cybersecurity greatest practices.
Threat Administration Frameworks and Instruments
A number of threat administration frameworks and instruments can be found to help efficient threat administration. These embrace the ISO 27005 threat administration customary, the NIST Cybersecurity Framework, and the COBIT threat administration framework. These frameworks and instruments present a structured method to threat administration, enabling organizations to establish, assess, and mitigate dangers successfully.
The common value of an information breach is $3.92 million, indicating the significance of efficient threat administration and information safety.
Examples of Threat Administration in Follow
Efficient threat administration is important in varied industries, together with finance, healthcare, and authorities. For instance, the monetary business makes use of strong threat administration frameworks to establish and mitigate potential monetary dangers, whereas the healthcare business invests in cybersecurity measures to guard delicate affected person information. Within the authorities sector, threat administration is important to make sure the safety and integrity of important infrastructure and delicate info.
Compliance and Regulatory Necessities
Compliance and regulatory necessities are important elements of IT asset administration. As organizations deal with delicate info and rely closely on know-how, they need to adhere to varied legal guidelines and rules to make sure the safety and integrity of their programs. Failure to conform can lead to extreme penalties, together with fines and reputational injury.
Regulatory necessities, such because the Basic Information Safety Regulation (GDPR) and the Well being Insurance coverage Portability and Accountability Act (HIPAA), govern how organizations handle and retailer delicate information. The GDPR, as an example, requires organizations to implement strong information safety measures to safeguard the private info of EU residents. Equally, HIPAA stipulates that healthcare organizations should adhere to strict tips for storing and sharing delicate affected person information.
Compliance with these rules is important, as non-compliance can result in substantial fines and reputational injury. For instance, the GDPR has imposed multi-million euro fines on organizations which have did not adjust to its necessities. Sustaining compliance requires organizations to spend money on strong IT asset administration practices, together with common audits, threat assessments, and safety updates.
### Varieties of Compliance Frameworks and Instruments
Organizations can leverage varied compliance frameworks and instruments to make sure they meet regulatory necessities. A few of these frameworks embrace:
Compliance Frameworks
Completely different compliance frameworks function tips for organizations to stick to. They outline the requirements and greatest practices for IT asset administration, guaranteeing that organizations meet regulatory necessities.
### Auditing and Remediation Software program
Auditing and remediation software program play an important position in sustaining compliance. These instruments allow organizations to establish vulnerabilities, assess dangers, and implement mandatory remediation measures to make sure they meet regulatory necessities.
Auditing Software program
Auditing software program helps organizations establish vulnerabilities and non-compliance dangers. Examples of auditing software program embrace:
– Compliance software program that analyzes system configurations and establish vulnerabilities
– Vulnerability evaluation instruments that present detailed studies on system weaknesses
Remediation Software program
Remediation software program allows organizations to handle recognized vulnerabilities and non-compliance dangers. Examples of remediation software program embrace:
– Patch administration instruments that automate software program updates and patch deployments
– Configuration administration instruments that allow organizations to trace and implement system modifications
### Finest Practices for Sustaining Compliance
Sustaining compliance requires organizations to prioritize common audits, threat assessments, and safety updates. Some greatest practices for sustaining compliance embrace:
Common Audits and Threat Assessments
Common audits and threat assessments allow organizations to establish vulnerabilities and tackle them earlier than they change into main points. This helps preserve compliance and ensures the safety and integrity of programs.
### Avoiding Non-Compliance Fines
Avoiding non-compliance fines is important for organizations that deal with delicate info. Sustaining regulatory compliance requires organizations to prioritize strong IT asset administration practices, together with common audits, threat assessments, and safety updates.
Significance of Compliance
Adhering to regulatory necessities, similar to GDPR and HIPAA, is essential for sustaining a optimistic repute and avoiding non-compliance fines. Investing in IT asset administration practices that prioritize compliance ensures that organizations meet regulatory necessities.
Fame and Compliance
A optimistic repute is important for attracting and retaining prospects, staff, and companions. Organizations that prioritize regulatory compliance exhibit their dedication to safety and integrity, fostering belief with stakeholders and enhancing their repute.
Key Takeaways
Sustaining regulatory compliance requires organizations to prioritize IT asset administration practices that concentrate on security, safety, and integrity. By adhering to regulatory necessities, similar to GDPR and HIPAA, organizations can keep away from non-compliance fines and preserve a optimistic repute.
Staffing and Coaching

On this hyper-digital period, IT asset administration has change into an indispensable element of any group. To navigate the advanced panorama of know-how, a talented and educated group is essential in guaranteeing that IT property are correctly managed, utilized, and optimized. Ample staffing and coaching not solely enhance effectivity but in addition stop potential dangers and monetary losses.
Having the precise expertise and coaching is important for efficient IT asset administration. The significance of coaching can’t be overstated, as IT professionals with insufficient coaching can result in misconfigured programs, inefficient processes, and potential information breaches. Furthermore, correct coaching allows IT asset managers to remain up-to-date with the most recent applied sciences and developments, permitting them to make knowledgeable selections and supply higher providers to stakeholders.
Roles and Duties
Two key roles are important in IT asset administration: Asset Managers and Stock Coordinators. Asset Managers are answerable for planning, organizing, and sustaining IT property, together with procurement, set up, and disposal. They have to make sure that property are correctly configured, up to date, and utilized to satisfy enterprise wants. Stock Coordinators, however, are answerable for monitoring and sustaining detailed information of IT property, together with their standing, location, and possession.
Coaching Applications and Certifications
A number of coaching applications and certifications can be found for IT asset administration professionals. The CompTIA IT Asset Administration (ITAM) certification is a notable instance, because it demonstrates a person’s information and expertise in IT asset administration greatest practices, together with stock administration, software program licensing, and asset lifecycle administration.
Recruiting and Retaining Expertise
Efficient recruitment and retention methods are essential in attracting and retaining prime expertise within the subject of IT asset administration. Organizations ought to search for professionals with related IT expertise, a confirmed observe report in IT asset administration, and powerful analytical, communication, and problem-solving expertise. Moreover, organizations ought to present ongoing coaching {and professional} growth alternatives to make sure that their staff keep up-to-date with the most recent applied sciences and developments.
Recruiting and retaining expertise in IT asset administration requires a strategic method. This entails making a optimistic work atmosphere, providing aggressive salaries and advantages, and offering alternatives for development {and professional} growth. Moreover, organizations ought to foster a tradition of collaboration and innovation, encouraging staff to share their concepts and ideas.
Some organizations have applied progressive recruitment methods to draw prime expertise in IT asset administration. As an example, they might supply versatile work preparations, skilled certifications, or alternatives for mentorship and coaching. These methods not solely enhance worker satisfaction but in addition improve productiveness and effectivity.
By prioritizing staffing and coaching, organizations can make sure that their IT property are correctly managed, utilized, and optimized. This, in flip, results in improved effectivity, diminished prices, and enhanced enterprise outcomes.
Expertise and Instruments
In at this time’s fast-paced digital panorama, IT asset administration depends closely on varied applied sciences and instruments to streamline processes, improve effectivity, and scale back prices. Because the business continues to evolve, the demand for strong and versatile IT asset administration programs grows, driving innovation and adoption of cutting-edge applied sciences. This delves into the totally different applied sciences and instruments used to help IT asset administration, highlighting their advantages, options, and examples of fashionable options.
IT Asset Administration Software program
IT asset administration software program performs an important position in automating and optimizing processes associated to {hardware} and software program stock administration, procurement, and disposal. By leveraging these instruments, organizations can considerably scale back guide labor, enhance visibility, and make knowledgeable selections based mostly on real-time information. This software program usually gives options similar to:
– Automated stock administration
– Actual-time monitoring and reporting
– Integration with present programs
– Customizable workflows and reporting
Some fashionable IT asset administration software program consists of:
– ServiceNow
– SAP
– AssetWorks
– Jamf
– Cherwell
These programs have been designed to cater to the varied wants of organizations, from small companies to massive enterprises, and supply scalability and adaptability to adapt to altering necessities.
{Hardware} and Software program Options
Along with software program options, {hardware} and software program elements are important instruments in IT asset administration. These elements allow organizations to gather, course of, and retailer information associated to property, making it simpler to trace and preserve stock.
–
- Barcode scanners and printers
- RFID tags and readers
- Good playing cards and card readers
- Cellular units and cellular apps
- Centralized servers and storage programs
These {hardware} elements work along with software program options to create a complete IT asset administration system.
Efficient IT asset administration depends on the mixing of {hardware} and software program instruments to supply real-time visibility and management over property.
Finest Practices for Evaluating and Deciding on IT Asset Administration Techniques
When evaluating and choosing an IT asset administration system, organizations ought to take into account the next components:
– Price and return on funding (ROI)
– Scalability and adaptability
– Integration with present programs
– Person expertise and help
– Information safety and compliance
- Assess present processes and establish areas for enchancment
- Outline necessities and priorities for the brand new system
- Analysis and consider obtainable options
- Conduct demos and pilots (if mandatory)
- Examine options, pricing, and help
- Make an knowledgeable determination based mostly on enterprise wants and objectives
By following these greatest practices, organizations can choose an IT asset administration system that aligns with their distinctive wants, supplies real-time visibility, and improves effectivity.
Change Administration
Change administration is a important facet of IT Asset Administration (ITAM) that entails managing IT asset-related modifications, similar to upgrades and retirements, to reduce disruption and guarantee enterprise continuity. Efficient change administration is important to make sure that all stakeholders are knowledgeable and affected by these modifications.
Significance of Change Administration, It asset administration greatest practices
Change administration frameworks and instruments, similar to change management processes and communication plans, are essential in managing IT asset-related modifications. These instruments assist organizations assess the affect of modifications on their IT infrastructure, establish potential dangers, and develop methods to mitigate them.
Change Administration Frameworks and Instruments
Change administration frameworks, similar to ITIL (Data Expertise Infrastructure Library), present a structured method to managing IT asset-related modifications. The ITIL framework emphasizes the significance of defining, planning, and implementing modifications in a method that minimizes disruption to enterprise operations.
| Framework | Description |
|---|---|
| ITIL | A extensively adopted framework for IT service administration, together with change administration. |
| COBIT | A framework for IT governance and administration, together with change administration and IT asset administration. |
Finest Practices for Conducting Change Impression Assessments
Conducting change affect assessments is important in figuring out potential dangers and creating methods to mitigate them. The next greatest practices might help organizations conduct efficient change affect assessments:
- Determine all stakeholders affected by the change.
- Assess the potential dangers and advantages of the change.
- Develop an in depth plan for implementing the change.
- Talk the change and its affect to all stakeholders.
- Monitor and consider the change’s affect on enterprise operations.
Creating Efficient Change Administration Plans
Creating efficient change administration plans is essential in minimizing disruption and guaranteeing enterprise continuity. The next steps might help organizations develop efficient change administration plans:
- Outline the change and its goals.
- Determine all stakeholders affected by the change.
- Assess the potential dangers and advantages of the change.
- Develop an in depth plan for implementing the change.
- Talk the change and its affect to all stakeholders.
- Monitor and consider the change’s affect on enterprise operations.
Change administration is a course of that entails planning, implementing, and reviewing modifications to make sure minimal disruption to enterprise operations.
Remaining Abstract
In conclusion, IT asset administration is a important facet of any group’s IT technique. By implementing efficient IT asset administration greatest practices, organizations can scale back prices, enhance effectivity, and mitigate dangers. This information has supplied a complete overview of the important thing elements of IT asset administration, from stock administration to steady enchancment. By following the most effective practices Artikeld on this information, organizations can make sure the efficient administration of their IT property and obtain their enterprise goals.
Detailed FAQs
What’s IT asset administration?
IT asset administration is the apply of monitoring, managing, and sustaining a company’s IT property, together with {hardware}, software program, and providers.
Why is IT asset administration necessary?
IT asset administration is necessary as a result of it helps organizations scale back prices, enhance effectivity, and mitigate dangers related to IT property.
What are the important thing elements of IT asset administration?
The important thing elements of IT asset administration embrace stock administration, asset lifecycle administration, value administration, threat administration, compliance and regulatory necessities, staffing and coaching, know-how and instruments, change administration, and steady enchancment.