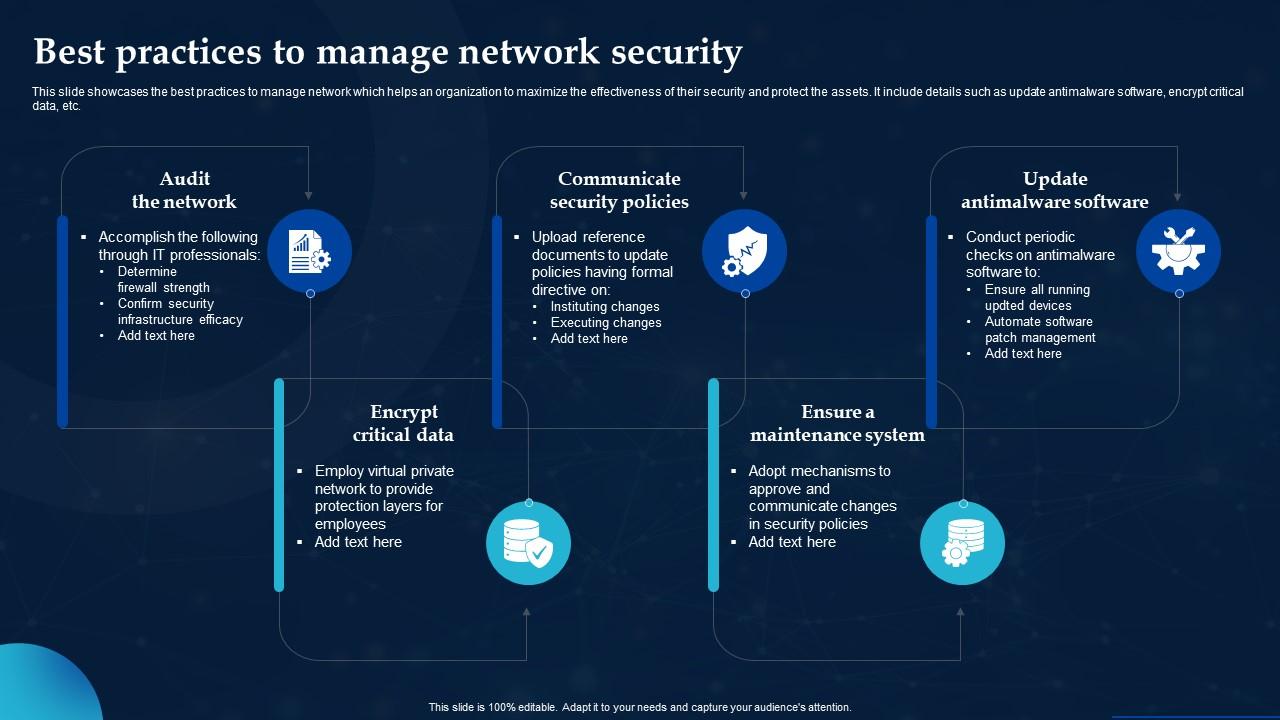
Community safety greatest practices units the stage for a complete understanding of the measures that may be taken to safeguard digital data and networks. A strong basis in community safety greatest practices is important in at present’s more and more complicated digital panorama, the place information breaches and cyber assaults have gotten extra frequent and complex.
The Artikel supplied provides a broad vary of subjects associated to community safety greatest practices, from entry management and authentication to community gadget safety and vulnerability administration. Every part delves into the intricacies of community safety, offering readers with an intensive understanding of the ideas and strategies vital to guard networks from numerous sorts of threats.
Community Safety Fundamentals: Community Safety Finest Practices
Community safety is a crucial facet of contemporary computing, safeguarding delicate data and stopping unauthorized entry to pc programs and networks. A complete strategy to community safety includes implementing numerous measures to guard in opposition to malicious actions, together with unauthorized entry, information breaches, and different cyber threats. On this part, we’ll focus on the significance of entry management, community segmentation, widespread community safety threats and vulnerabilities, and the position of firewalls in community safety.
Entry Management
Entry management is a elementary facet of community safety, specializing in regulating person entry to community assets and information. Efficient entry management ensures that solely approved people have entry to delicate data and system assets. That is sometimes achieved by means of the usage of authentication mechanisms, resembling username/password combos, sensible playing cards, or biometric authentication.
Entry management is carried out utilizing a set of insurance policies and procedures that outline person roles, entry rights, and permissions. These insurance policies have to be recurrently reviewed and up to date to make sure they continue to be efficient and compliant with organizational safety insurance policies. Entry management measures may be categorized into three major sorts:
- The necessity-to-know precept: Customers are granted entry solely to data and assets essential to carry out their job capabilities.
- The least privilege precept: Customers are granted the minimal set of privileges required to carry out their job capabilities.
- Separation of duties: Completely different people or teams are chargeable for performing crucial operations, guaranteeing that no single particular person can compromise safety.
Community Segmentation
Community segmentation includes dividing a community into smaller segments or sub-networks, every with its personal set of safety insurance policies and entry controls. This strategy improves community safety by decreasing the assault floor and limiting the unfold of malware and different safety threats.
Community segmentation may be carried out utilizing numerous strategies, together with:
- Digital LANs (VLANs): Sub-networks are created utilizing VLANs, that are remoted from one another utilizing network-layer (Layer 3) switching.
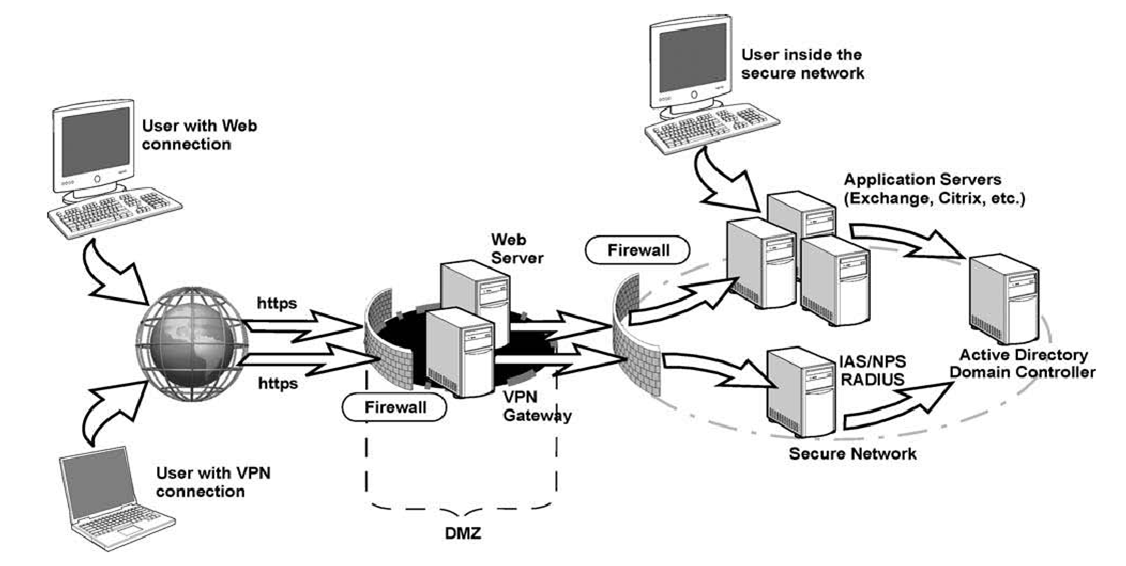
- Digital Non-public Networks (VPNs): VPNs are used to create safe, encrypted connections between two or extra networks.
Frequent Community Safety Threats and Vulnerabilities
Community safety threats and vulnerabilities may be categorized into a number of sorts, together with:
- Malware: Software program designed to hurt or exploit a pc system, resembling viruses, worms, and trojans.
- Denial-of-service (DoS) and distributed denial-of-service (DDoS) assaults: Overwhelming a community or system with site visitors or requests to render it inaccessible.
- Phishing: Makes an attempt to trick customers into revealing delicate data or performing malicious actions.
Position of Firewalls in Community Safety
Firewalls are community safety programs that monitor and management incoming and outgoing community site visitors based mostly on predetermined safety guidelines. They play an important position in defending networks from unauthorized entry and malicious actions.
Firewalls may be categorized into two major sorts:
- Community firewalls: Examine community site visitors and block malicious or unauthorized entry makes an attempt.
- Host-based firewalls: Put in on particular person computer systems, these firewalls examine and regulate site visitors on a per-host foundation.
Firewalls may be configured to dam or enable incoming and outgoing site visitors based mostly on a wide range of elements, together with:
- IP addresses and ports
- Protocols (e.g., HTTP, FTP)
- Supply and vacation spot IP addresses
Firewalls may also be configured to implement community handle translation (NAT), which permits a number of non-public IP addresses to be mapped to a single public IP handle, bettering community safety and decreasing the assault floor.
Authentication and Authorization

Authentication and authorization are two distinct ideas in community safety that make sure the integrity and safety of knowledge and programs. Authentication refers back to the technique of verifying the id of a person or system, whereas authorization determines what actions a official person or system can carry out.
Forms of Authentication Strategies
There are three major sorts of authentication strategies utilized in community safety: passwords, biometrics, and sensible playing cards.
- Password-based authentication is essentially the most generally used technique. A password is a secret string of characters identified solely to the person that’s supplied to the system to realize entry. Passwords ought to be not less than 12 characters lengthy, embrace a mixture of uppercase and lowercase letters, digits, and particular characters, and shouldn’t be simply guessable or just like any earlier passwords.
- Biometric authentication includes the usage of bodily or behavioral traits resembling fingerprints, facial recognition, or iris scans to establish a person. This technique gives a excessive degree of safety and is troublesome to duplicate or bypass.
- Good card-based authentication includes the usage of a card with a built-in microprocessor that shops encryption keys and certificates. The cardboard is used to authenticate and authorize customers, and it gives a further layer of safety.
Position-Based mostly Entry Management (RBAC)
Position-Based mostly Entry Management (RBAC) is a safety strategy that assigns permissions to customers based mostly on their position inside a company. The concept behind RBAC is to assign a set of permissions to a selected position after which assign that position to a person. This makes it simpler to handle entry and permissions for big numbers of customers.
Position-Based mostly Entry Management (RBAC) is outlined as “A safety strategy that assigns permissions to customers based mostly on their position inside a company.”
Implementing Multi-Issue Authentication
Implementing multi-factor authentication (MFA) includes utilizing a couple of issue to confirm the id of a person. This may embrace a mixture of one thing a person is aware of (resembling a password), one thing a person has (resembling a wise card), and one thing the person is (resembling a fingerprint).
- One-Time Passwords (OTPs): An OTP is a password that’s legitimate for under a brief interval, making it troublesome for attackers to make use of. OTPs may be despatched through SMS or generated by an authenticator app.
- Banking Tokens: A financial institution token is a small gadget that generates a singular password that modifications steadily, including an additional layer of safety.
- U2F: U2F stands for Common 2nd Issue, which makes use of a {hardware} token, resembling a USB gadget, to confirm a person’s id.
- MFA Apps: MFA apps, resembling Google Authenticator or Authy, generate time-based OTPs that can be utilized to authenticate a person.
Usually Updating and Rotating Passwords
Usually updating and rotating passwords is important to take care of the safety of a system. This includes altering passwords recurrently and utilizing a password supervisor to maintain observe of a number of passwords.
- Passwords ought to be modified not less than each 60 to 90 days, and this ought to be performed mechanically by the system.
- Passwords ought to be complicated, together with a mixture of uppercase and lowercase letters, digits, and particular characters.
- Password managers can be utilized to generate and retailer complicated passwords, making it simpler to handle a number of passwords.
Community Safety Protocols
Community safety protocols play an important position in guaranteeing the confidentiality, integrity, and availability of community communications. These protocols present a safe technique to transmit information over the web and defend in opposition to unauthorized entry, eavesdropping, and information tampering.
Distinction between IPv4 and IPv6
IPv4 (Web Protocol model 4) and IPv6 (Web Protocol model 6) are two variations of the web protocol used for routing site visitors on the web. IPv4 makes use of 32-bit addresses, whereas IPv6 makes use of 128-bit addresses. This main distinction permits IPv6 to offer a nearly limitless variety of IP addresses, making it an important improve for the ever-growing web.
IPv4 addresses are represented in a dotted decimal format, resembling 192.0.2.1, whereas IPv6 addresses are represented in a hexadecimal format, resembling 2001:0db8:85a3:0000:0000:8a2e:0370:7334. This improve in handle house allows IPv6 to deal with the rising variety of units and supply extra options, resembling improved safety and high quality of service.
Significance of Safe Sockets Layer/Transport Layer Safety (SSL/TLS)
SSL/TLS (Safe Sockets Layer/Transport Layer Safety) is a cryptographic protocol that gives safe communication between an online server and a consumer, resembling an online browser. It ensures the confidentiality, integrity, and authenticity of knowledge exchanged between the server and the consumer, defending in opposition to eavesdropping, tampering, and man-in-the-middle assaults.
SSL/TLS works by encrypting information utilizing a symmetric key, which is shared between the server and the consumer. This encrypted information is then transmitted over the web, guaranteeing that solely the meant events can decrypt and entry it. SSL/TLS is broadly utilized in e-commerce, on-line banking, and different safe on-line transactions.
Implementing Digital Non-public Networks (VPNs)
A Digital Non-public Community (VPN) is a safe community connection between two or extra units over the web. It gives a personal and safe tunnel for information transmission, encrypting information and defending in opposition to unauthorized entry.
To implement a VPN, the next steps are adopted:
- Set up and configure VPN software program or {hardware} on the gadget.
- Set up a safe connection to the VPN server.
- Authenticate the person with a username and password or different authentication technique.
- Encrypt information and transmit it over the VPN tunnel.
Position of Web Protocol Safety (IPSec) in community safety
IPSec (Web Protocol Safety) is a collection of protocols that gives safety for IP communications by encrypting and authenticating information. It gives a safe technique for transmitting IP packets between units, defending in opposition to unauthorized entry and information tampering.
IPSec consists of two protocols: Authentication Header (AH) and Encapsulating Safety Payload (ESP). AH gives authentication and integrity, guaranteeing that information just isn’t tampered with, whereas ESP gives confidentiality by encrypting information.
Configuring community safety protocols on widespread community units
Community units, resembling routers and switches, may be configured to implement community safety protocols, resembling ACLs, firewall guidelines, and VPN configurations.
To configure community units, observe these steps:
- Login to the gadget’s internet interface or command-line interface.
- Navigate to the safety or firewall configuration web page.
- Configure ACLs or firewall guidelines to permit or deny particular site visitors.
- Configure VPN settings, resembling server IP handle and authentication technique.
Wi-fi Community Safety
Wi-fi community safety is a crucial element of community safety, as wi-fi networks are more and more getting used to attach units and supply entry to community assets. Wi-fi networks provide the comfort of mobility, however additionally they introduce new safety dangers. On this part, we’ll focus on the fundamentals of wi-fi networking, the significance of WPA2 (or WPA3) encryption, configuring wi-fi community entry management, the position of wi-fi intrusion detection programs (WIDS), and securing wi-fi community entry factors (APs).
Fundamental Ideas of Wi-fi Networking
Wi-fi networking makes use of radio waves to transmit information between units. The commonest wi-fi networking know-how is Wi-Fi, which makes use of the two.4 GHz and 5 GHz frequency bands. Wi-Fi units use a method known as spread-spectrum to transmit information over the airwaves.
Significance of WPA2 (or WPA3) Encryption for Wi-fi Networks
WPA2 (or WPA3) encryption is a crucial element of wi-fi community safety. WPA2 makes use of a symmetric key algorithm to encrypt information, whereas WPA3 makes use of a brand new algorithm known as ChaCha20-Poly1305. WPA2 encryption ensures that information transmitted over the airwaves is safe and can’t be intercepted by unauthorized units. WPA3 encryption gives even stronger safety and is a advisable improve for wi-fi networks.
- WPA2 and WPA3 encryption present a minimal of 128-bit encryption power, offering sturdy safety in opposition to unauthorized entry.
- WPA2 and WPA3 encryption use a method known as TKIP (Temporal Key Integrity Protocol) to stop replay assaults and guarantee safe key change.
Blockquote: “A safe wi-fi community is one which makes use of sturdy encryption, safe password insurance policies, and up-to-date encryption protocols.” (Supply: IEEE 802.11i normal)
Configuring Wi-fi Community Entry Management
Wi-fi community entry management refers back to the technique of controlling who can entry a wi-fi community and what assets they’ll entry. Configuring wi-fi community entry management includes organising a RADIUS (Distant Authentication Dial-In Person Service) server to authenticate customers earlier than granting them entry to the community. The RADIUS server can use a wide range of authentication strategies, resembling username and password, sensible playing cards, or biometric scanners.
Position of Wi-fi Intrusion Detection Techniques (WIDS)
Wi-fi intrusion detection programs (WIDS) are software program or {hardware} home equipment designed to detect and forestall wi-fi assaults. WIDS programs monitor the airwaves for suspicious exercise, resembling unauthorized entry makes an attempt or malware transmission.
Securing Wi-fi Community Entry Factors (APs)
Securing wi-fi community entry factors (APs) requires a mixture of bodily and logical safety measures. Bodily safety measures embrace bodily securing the AP to stop tampering or theft. Logical safety measures embrace configuring the AP to make use of WPA2 (or WPA3) encryption, organising a RADIUS server, and configuring the AP for visitor entry.
| Advantages of Securing Wi-fi Community Entry Factors (APs) | ||
|---|---|---|
| Prevents unauthorized entry makes an attempt | Helps to stop malware transmission | Protects delicate information |
Finest Practices for Securing Wi-fi Networks
To safe wi-fi networks, observe these greatest practices:
- Use WPA2 (or WPA3) encryption for all wi-fi networks
- Configure wi-fi community entry management to require customers to authenticate earlier than having access to the community
- Usually replace software program and firmware for all wi-fi community units
- Implement a WIDS system to detect and forestall wi-fi assaults
Information Backup and Restoration
Information backup and restoration are essential elements of a complete community safety technique. Shedding necessary information may be devastating for organizations, making it important to implement common information backups and have a dependable information restoration plan in place.
Efficient information backup and restoration processes be certain that enterprise continuity is maintained, even within the occasion of a catastrophe. On this part, we’ll discover the significance of normal information backups, focus on numerous information restoration strategies, and study widespread information backup and restoration instruments.
Significance of Common Information Backups
Common information backups are important for safeguarding in opposition to information loss on account of numerous causes resembling {hardware} failure, software program corruption, human error, or pure disasters. With common backups, you’ll be able to be certain that your information is secure and may be restored shortly within the occasion of a catastrophe.
- Information backups present a security internet in opposition to information loss, permitting you to revive your information shortly and decrease downtime.
- Common backups be certain that your information is up-to-date, decreasing the danger of knowledge inconsistencies and errors.
- Information backups present a backup of your information, permitting you to check and validate your backups recurrently.
Information Restoration Strategies
Information restoration strategies contain strategies used to get better information from backups or secondary storage units. Snapshotting and replication are two widespread information restoration strategies utilized in community safety.
Snapshotting includes creating a duplicate of knowledge at a selected time limit, permitting for fast restoration within the occasion of a catastrophe.
- Snapshots present a point-in-time copy of knowledge, making it simpler to get better information from a selected time limit.
- Snapshots scale back the danger of knowledge corruption and inconsistencies, guaranteeing that your information is constant and dependable.
Information Backup and Restoration Instruments
Numerous information backup and restoration instruments can be found, together with software program and {hardware} options. These instruments assist streamline the information backup and restoration course of, making it simpler to guard and get better information.
- Software program options, resembling backup software program, can automate information backups and recoveries, decreasing the danger of human error.
- Cloud-based backup options enable for distant information backups and recoveries, making it simpler to handle information throughout a number of areas.
Position of Information Backup and Restoration in Catastrophe Restoration Planning
Information backup and restoration play an important position in catastrophe restoration planning, guaranteeing enterprise continuity within the occasion of a catastrophe.
- Information backups present a way of recovering information shortly, minimizing downtime and decreasing the danger of knowledge loss.
- Information restoration plans be certain that enterprise operations can proceed even within the occasion of a catastrophe.
Securing Information Backups and Restoration Processes
Securing information backups and restoration processes is important to stop information breaches and unauthorized entry.
- Use safe protocols, resembling encryption, to guard information backups and recoveries.
- Implement entry controls and authorization mechanisms to make sure that solely approved personnel can entry information backups and recoveries.
Vulnerability Administration
Vulnerability administration is a crucial facet of community safety that includes figuring out, prioritizing, and addressing vulnerabilities in a company’s programs, functions, and infrastructure. Efficient vulnerability administration requires a proactive strategy to cut back the danger of safety breaches and information theft.
The Position of Vulnerability Evaluation Instruments in Community Safety
Vulnerability evaluation instruments play an important position in vulnerability administration by serving to organizations establish and prioritize vulnerabilities of their programs and functions. These instruments use numerous strategies, resembling community scanning, vulnerability scanning, and configuration evaluation, to establish potential vulnerabilities and supply suggestions for remediation.
Standard vulnerability evaluation instruments embrace Nessus, OpenVAS, and Qualys.
Vulnerability evaluation instruments can assist organizations establish vulnerabilities earlier than they’re exploited by attackers, decreasing the danger of safety breaches and information theft.
The Significance of Usually Scanning for Vulnerabilities
Common vulnerability scanning is important to make sure that a company’s programs and functions are safe and free from vulnerabilities. Vulnerability scanning ought to be carried out regularly, ideally weekly or month-to-month, to establish new vulnerabilities and assess the effectiveness of current remediation efforts.
- Vulnerability scans assist establish new vulnerabilities that will have been launched by means of updates, patches, or new software program installations.
- Vulnerability scans assess the effectiveness of current remediation efforts and supply suggestions for additional enchancment.
- Vulnerability scans assist establish vulnerabilities that will have been neglected or missed throughout earlier scans.
Figuring out and Prioritizing Vulnerabilities, Community safety greatest practices
Figuring out and prioritizing vulnerabilities is a crucial step in vulnerability administration. Vulnerabilities ought to be prioritized based mostly on their severity, exploitability, and potential affect on the group.
- Vulnerabilities ought to be prioritized based mostly on their Frequent Vulnerability Scoring System (CVSS) rating, which assesses the severity and exploitability of the vulnerability.
- Vulnerabilities ought to be prioritized based mostly on their potential affect on the group, together with the potential for information theft, disruption of enterprise operations, or reputational injury.
- Vulnerabilities ought to be prioritized based mostly on the chance of exploitation by attackers.
Examples of Frequent Vulnerability Administration Instruments
A number of well-liked vulnerability administration instruments can be found, together with:
- Nessus: A complete vulnerability scanning software that gives detailed data on vulnerabilities and proposals for remediation.
- OpenVAS: An open-source vulnerability scanning software that gives a complete vulnerability administration platform.
- Qualys: A cloud-based vulnerability administration platform that gives vulnerability scanning, remediation suggestions, and steady monitoring.
The Position of Vulnerability Administration in Incident Response Planning
Vulnerability administration performs a crucial position in incident response planning by serving to organizations establish and mitigate vulnerabilities that could be exploited by attackers.
- Vulnerability administration helps establish vulnerabilities that could be exploited by attackers, permitting organizations to take proactive measures to mitigate the danger.
- Vulnerability administration helps assess the potential affect of a safety breach, together with the potential for information theft, disruption of enterprise operations, or reputational injury.
- Vulnerability administration helps establish alternatives for steady enchancment in safety controls and procedures.
Compliance and Governance
Compliance and governance are crucial elements of a sturdy community safety technique. Efficient compliance and governance assist organizations be certain that they’re assembly regulatory necessities, minimizing the danger of safety breaches, and sustaining confidentiality, integrity, and availability (CIA) of delicate information.
### Significance of Compliance with Regulatory Necessities
Regulatory necessities resembling HIPAA (Well being Insurance coverage Portability and Accountability Act) and PCI-DSS (Fee Card Business Information Safety Commonplace) are in place to guard delicate information and forestall safety breaches. Compliance with these rules is important for organizations dealing with delicate information. Failure to conform can lead to vital fines and reputational injury.
Compliance necessities could embrace:
Make sure the confidentiality, integrity, and availability of delicate information as per regulatory necessities.
### Position of Governance Frameworks in Community Safety
Governance frameworks resembling COBIT (Management Aims for Data and Associated Know-how) and ITIL (Data Know-how Infrastructure Library) present a construction for organizations to handle and govern their IT assets successfully. These frameworks assist organizations align their IT technique with enterprise goals, guaranteeing that community safety is an integral a part of the general governance framework.
Key areas ruled by COBIT and ITIL embrace:
*
Danger Administration
Danger administration is a crucial element of community safety governance. It includes figuring out, assessing, and mitigating potential dangers to the group’s IT assets. Danger administration helps organizations prioritize their safety efforts and be certain that they’re investing in risk-reducing measures successfully.
Service Administration
Service administration is one other key space ruled by COBIT and ITIL. It includes managing IT companies to fulfill the wants of the enterprise, guaranteeing that they’re safe, obtainable, and dependable. Service administration helps organizations be certain that their community safety is aligned with enterprise goals and that safety measures are built-in into service supply.
Data Safety Administration
Data safety administration is a crucial element of community safety governance. It includes managing data safety to guard delicate information and forestall safety breaches. Data safety administration helps organizations be certain that their community safety is aligned with regulatory necessities and that safety measures are efficient in stopping safety breaches.
### Implementing Compliance and Governance Finest Practices in Community Safety
To implement compliance and governance greatest practices in community safety, organizations ought to:
-
Set up a transparent community safety coverage that Artikels the group’s safety goals, roles, and obligations.
-
Implement a threat administration framework that identifies, assesses, and mitigates potential dangers to the group’s IT assets.
-
Develop an incident response plan that Artikels procedures for responding to safety incidents.
-
Conduct common safety audits to make sure compliance with regulatory necessities and establish areas for enchancment.
-
Preserve correct data of security-related incidents and compliance actions.
### Significance of Steady Monitoring and Reporting in Community Safety
Steady monitoring and reporting are important elements of a sturdy community safety technique. They assist organizations establish safety incidents early, reply shortly, and keep compliance with regulatory necessities.
Key advantages of steady monitoring and reporting embrace:
*
Early Detection of Safety Incidents
Steady monitoring helps organizations detect safety incidents early, decreasing the danger of knowledge breaches and reputational injury.
Improved Incident Response
Steady monitoring allows organizations to reply shortly to safety incidents, decreasing the scope of injury and minimizing downtime.
Compliance with Regulatory Necessities
Steady monitoring helps organizations keep compliance with regulatory necessities, decreasing the danger of fines and reputational injury.
### Addressing Compliance and Governance in Community Safety Audits
Community safety audits assist organizations establish areas of non-compliance with regulatory necessities and assess the effectiveness of their safety measures. Key areas audited embrace:
-
Compliance with regulatory necessities resembling HIPAA, PCI-DSS, and GDPR.
-
Effectiveness of threat administration and incident response procedures.
-
Safety measures in place to guard delicate information and forestall safety breaches.
-
Compliance with governance frameworks resembling COBIT and ITIL.
-
Effectiveness of steady monitoring and reporting procedures.
Abstract
In conclusion, community safety greatest practices are an important element of sustaining a safe on-line presence. By understanding the significance of entry management, authentication, and community segmentation, amongst different measures, organizations can considerably scale back their vulnerability to cyber assaults and information breaches. Moreover, adopting greatest practices in community gadget safety, information backup and restoration, and vulnerability administration can assist organizations get better shortly and effectively within the occasion of an incident.
FAQ Abstract
Q: What’s the major operate of entry management in community safety?
A: The first operate of entry management in community safety is to manage and limit person entry to delicate areas of the community, based mostly on their identities or roles.
Q: How can multi-factor authentication improve community safety?
A: Multi-factor authentication can improve community safety by requiring customers to offer a number of types of verification, resembling a password and a biometric scan, making it harder for unauthorized customers to realize entry to the community.
Q: What’s the significance of recurrently updating and rotating passwords in community safety?
A: Usually updating and rotating passwords in community safety is important in stopping password-based assaults, resembling cracking and phishing, and guaranteeing that passwords usually are not shared or compromised.
Q: How can firewalls be used to boost community safety?
A: Firewalls can be utilized to dam or filter incoming and outgoing community site visitors, based mostly on predetermined safety guidelines, to stop unauthorized entry, malware, and different sorts of community threats.
Q: What’s the position of VPNs in community safety?
A: VPNs play an important position in community safety by making a safe and encrypted connection between the person’s gadget and the community, permitting customers to entry delicate information from distant areas with out compromising the community.