OWASP Webhook Safety Finest Practices is an important side of contemporary net improvement, guaranteeing the safe supply of notifications and knowledge between net functions. With the rise of webhook-based integrations, securing these endpoints has develop into a high precedence for builders. On this article, we’ll delve into the significance of webhook safety, the position of OWASP in selling safe coding practices, and the very best practices for implementing safe webhooks.
We’ll cowl varied elements of webhook safety, together with authentication and authorization, knowledge validation and sanitization, price limiting and IP blocking, error dealing with and logging, and safe webhook protocols and implementations. By the top of this dialogue, you’ll have a complete understanding of OWASP Webhook Safety Finest Practices and be outfitted to implement safe webhooks in your individual tasks.
OWASP Webhook Safety Finest Practices

In as we speak’s fashionable net improvement panorama, webhooks have develop into an integral part of communication between varied functions. Webhooks allow techniques to inform one another about occasions or updates, permitting for extra environment friendly and real-time interactions. Nonetheless, this elevated reliance on webhooks additionally brings about important safety issues, making it essential for builders to stick to greatest practices and tips to make sure the safety and integrity of webhooks.
The Open Internet Utility Safety Challenge (OWASP) performs an important position in selling safe coding practices and offering steering on varied security-related subjects, together with webhook safety. By following OWASP’s suggestions and requirements, builders can make sure the safety and trustworthiness of their webhooks.
The Significance of Safe Webhooks
Safe webhooks are essential for sustaining the integrity of knowledge and stopping unauthorized entry to delicate info. An insecure webhook can result in catastrophic penalties, equivalent to knowledge breaches, unauthorized transactions, and even the compromise of whole techniques. Due to this fact, it’s important to prioritize safe webhook improvement and deployment.
-
Be certain that all webhooks are correctly authenticated and approved to stop unauthorized entry.
Authenticating and authorizing webhooks ensures that solely meant events can ship and obtain occasions.
This may be achieved by varied strategies, equivalent to token-based authentication, SSL/TLS encryption, and even {custom} authentication mechanisms.
-
Implement safe protocols for webhook transmission, equivalent to HTTPS (TLS) to stop eavesdropping, tampering, and manipulation of webhook knowledge.
Encryption Technique Description HTTPS (TLS) Encrypts webhook knowledge in transit to stop unauthorized entry and eavesdropping. -
Usually monitor and audit webhook transactions to detect potential safety points or unauthorized exercise.
-
Common monitoring helps establish potential safety vulnerabilities and permits immediate motion to be taken.
Monitoring could be achieved with varied instruments and strategies, equivalent to logging, alerts, and even custom-built scripts. -
Auditing webhook transactions ensures that every one occasions are correctly accounted for, stopping unauthorized or sudden exercise.
Auditing processes ought to embrace verification of occasion authenticity, integrity, and consistency.
-
Common monitoring helps establish potential safety vulnerabilities and permits immediate motion to be taken.
OWASP’s Function in Selling Webhook Safety
OWASP supplies complete steering and assets on webhook safety, together with greatest practices, tips, and instruments to assist builders make sure the safety and integrity of their webhooks. By adhering to OWASP’s suggestions and requirements, builders may help forestall widespread webhooks vulnerabilities and keep the trustworthiness of their functions.
OWASP’s mission is to offer free and open-source information that’s constantly up to date by a worldwide neighborhood of specialists.
Some notable OWASP assets for webhook safety embrace:
* The OWASP Webhooks Safety Cheat Sheet supplies a complete information to securing webhooks, together with authentication, authorization, and different essential safety issues.
* The OWASP Webhook Authentication Information provides detailed suggestions for implementing safe authentication mechanisms for webhooks.
Authentication and Authorization Finest Practices
Authentication and authorization are two very important ideas in guaranteeing the safety of webhooks. Whereas typically used interchangeably, they serve distinct functions in defending delicate knowledge and features.
Authentication is the method of verifying a consumer’s identification, guaranteeing that solely approved entities can work together with the system. However, authorization is about granting or denying entry to particular assets or features based mostly on a validated identification. Each are indispensable for safeguarding towards unauthorized entry and sustaining knowledge integrity.
Variations between Authentication and Authorization, Owasp webhook safety greatest practices
The first distinction between authentication and authorization lies of their aims.
- Authentication focuses on verifying the identification of customers or entities, guaranteeing that they’re who they declare to be.
- Authorization, however, is anxious with granting or denying entry to particular assets or features based mostly on a validated identification.
For instance this distinction, contemplate a financial institution’s system. Authentication would contain validating a consumer’s login credentials (username and password) to make sure they’ll entry their account. Authorization, on this case, would decide whether or not the consumer has the required permissions to carry out particular actions, equivalent to withdrawing cash or updating account settings.
Significance of Safe Authentication Protocols
On the subject of authentication, safety is paramount. Safe authentication protocols make sure that delicate info stays confidential and tamper-proof. One widespread and safe authentication protocol is JSON Internet Tokens (JWT).
JSON Internet Tokens (JWT) are digitally signed tokens that include a payload of consumer knowledge. They’re encrypted utilizing a secret key and could be verified by the recipient utilizing the identical key.
JWT provides a number of advantages, together with:
- Statelessness: JWT doesn’t retailer any state on the server-side, lowering the chance of knowledge breaches.
- Token-based authentication: JWT tokens can be utilized as a substitute of conventional session-based authentication, making it simpler to handle consumer classes.
- Scalability: JWT can deal with excessive site visitors and enormous consumer bases with ease.
Examples of Safe Authorization Practices
Authorization practices make sure that customers have entry to the assets and features they should carry out their duties. Function-Based mostly Entry Management (RBAC) is a well-liked authorization follow.
RBAC is a mannequin that assigns customers to roles based mostly on their job features. Every position is granted entry to particular assets and features, guaranteeing that customers solely have the required permissions to carry out their duties.
Function-Based mostly Entry Management (RBAC) ensures that customers have entry to assets and features based mostly on their roles.
RBAC provides a number of advantages, together with:
| Advantages | Description |
|---|---|
| Improved safety | RBAC reduces the chance of unauthorized entry and knowledge breaches by limiting consumer permissions. |
| Enhanced productiveness | RBAC streamlines consumer entry and reduces the executive burden of managing permissions. |
| Elevated flexibility | RBAC permits for simple changes to consumer roles and permissions as enterprise wants change. |
Knowledge Validation and Sanitization
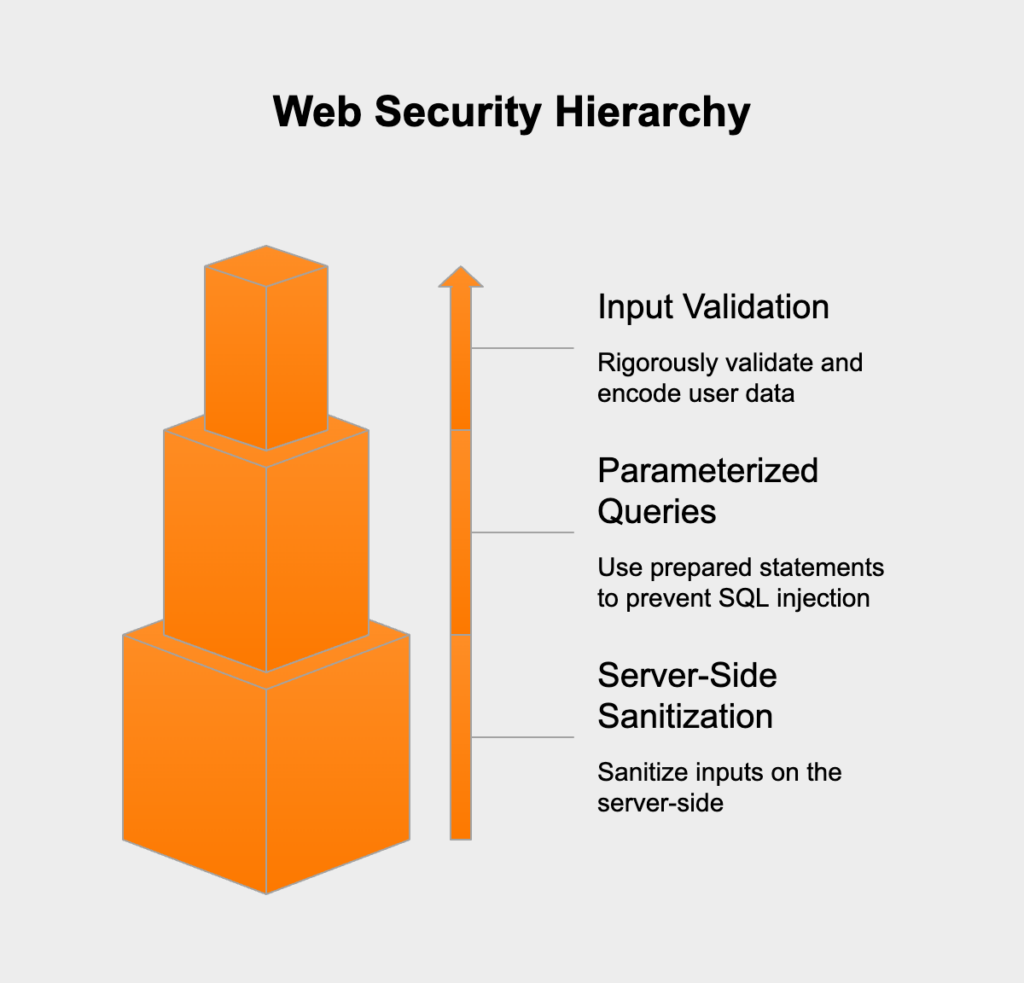
Knowledge validation and sanitization are essential parts of webhook safety, as they assist forestall malicious knowledge from being accepted and processed by the receiver finish. This reduces the chance of webhooks being exploited for varied malicious functions equivalent to knowledge breaches or assaults. Guaranteeing that solely validated and sanitized knowledge is processed can forestall a variety of safety points.
Knowledge validation refers back to the means of verifying that the incoming knowledge conforms to anticipated codecs and buildings. This consists of checking the info kind, size, and contents to make sure it meets the required necessities. For example, in a webhook that sends consumer knowledge, the validation course of can confirm that the consumer’s electronic mail tackle accommodates solely alphanumeric characters and doesn’t exceed a sure size.
Sorts of Knowledge Validation
There are two main forms of knowledge validation: enter validation and output validation.
### Enter validation
Enter validation entails verifying the format and contents of the incoming knowledge earlier than it’s processed. This helps forestall malicious knowledge from being accepted and reduces the chance of safety points equivalent to knowledge breaches or SQL injection assaults.
In enter validation, it’s important to confirm the format and construction of the incoming knowledge to make sure it meets the anticipated necessities.
### Output validation
Output validation, however, entails verifying the format and contents of the info after it has been processed. This helps make sure that the validated knowledge is correct and full.
Safe Knowledge Sanitization Practices
Knowledge sanitization entails eradicating or modifying delicate info from the info to stop it from being compromised. Listed here are some examples of safe knowledge sanitization practices:
– Eradicating delicate info: This entails eradicating delicate info equivalent to bank card numbers, passwords, and private identifiable info (PII) from the info.
– Encrypting delicate info: This entails encrypting delicate info utilizing safe encryption algorithms to stop unauthorized entry.
– Utilizing whitelisting: This entails solely accepting knowledge that matches a particular format or construction, thereby stopping malicious knowledge from being accepted.
Knowledge Sanitization Examples
Listed here are some examples of safe knowledge sanitization practices:
–
- Eradicating bank card numbers and expiration dates from the info
- Encrypting delicate info, equivalent to passwords and PII, utilizing safe encryption algorithms
- Utilizing whitelisting to solely settle for knowledge that matches a particular format or construction
- Eradicating private identifiable info (PII) equivalent to names, addresses, and cellphone numbers from the info
Finest Practices for Knowledge Sanitization
Listed here are some greatest practices for knowledge sanitization:
–
- All the time encrypt delicate info utilizing safe encryption algorithms
- Use whitelisting to solely settle for knowledge that matches a particular format or construction
- Take away or modify delicate info, equivalent to bank card numbers and PII, from the info
- Solely permit approved personnel to entry and modify delicate knowledge
- Usually assessment and replace knowledge sanitization insurance policies and procedures to make sure they continue to be efficient
Price Limiting and IP Blocking
Price limiting and IP blocking are essential mechanisms in stopping webhook abuse. Webhook abuse can result in unauthorized entry, knowledge breaches, and different safety dangers. Price limiting and IP blocking assist to mitigate these dangers by limiting the frequency and supply of incoming webhook requests.
Price limiting entails imposing a restrict on the variety of requests that may be made inside a particular timeframe. This may be based mostly on the IP tackle, consumer ID, or different components. IP blocking, however, entails blocking particular IP addresses which might be identified to be related to malicious exercise.
Sort of Price Limiting
There are two principal forms of price limiting: time-based price limiting and IP-based price limiting.
-
Time-based price limiting entails imposing a restrict on the variety of requests that may be made inside a particular timeframe, whatever the supply. This may be based mostly on a sliding window strategy, the place the window strikes ahead over time, or a set window strategy, the place the window is fastened in dimension.
IP-based price limiting entails imposing a restrict on the variety of requests that may be made out of a particular IP tackle or vary of IP addresses inside a particular timeframe. This may be based mostly on IP tackle, subnet, or different network-level components.
-
Time-based price limiting supplies a extra generalized strategy, because it doesn’t require information of the supply IP tackle. Nonetheless, it might not be efficient in blocking focused assaults, the place an attacker makes use of a distinct IP tackle or supply for every request.
IP-based price limiting supplies a extra focused strategy, as it may block particular IP addresses related to malicious exercise. Nonetheless, it might not be efficient in blocking distributed assaults, the place a number of IP addresses are concerned.
Instance of IP Blocking
IP blocking entails blocking particular IP addresses which might be identified to be related to malicious exercise. This may be performed utilizing varied instruments and strategies, together with IP blocking lists, firewall guidelines, and net utility firewalls.
IP blocking is an efficient mechanism for stopping webhook abuse, as it may block a variety of malicious exercise.
-
Utilizing third-party IP blocking lists, equivalent to these supplied by Spamhaus or Google’s reCAPTCHA, may help to dam identified malicious IP addresses.
Configuring firewall guidelines to dam particular IP addresses or IP tackle ranges may help to stop focused assaults.
Utilizing net utility firewalls to dam particular IP addresses or IP tackle ranges may help to stop distributed assaults.
Error Dealing with and Logging
Error dealing with and logging are essential parts of webhook safety, as they allow builders to establish and tackle potential vulnerabilities of their techniques. Correct error dealing with and logging additionally assist organizations meet regulatory necessities and keep compliance with trade requirements.
Sorts of Error Dealing with
There are two main forms of error dealing with: generic error messages and exception messages.
– Generic Error Messages: A lot of these error messages don’t present particular particulars concerning the error that occurred. They typically include generic info, equivalent to “Error occurred” or “Inner Server Error.”
– Exception Messages: Exception messages, however, present detailed details about the error that occurred. They typically include particular particulars concerning the error, equivalent to its supply and doable options.
Safe Logging Practices
- Centralized Log Administration System
A centralized log administration system permits organizations to gather, retailer, and analyze logs from varied sources in a single location. This helps enhance incident response instances, scale back the chance of knowledge breaches, and make it simpler to adjust to regulatory necessities.
-
Logging Delicate Data
It’s important to log delicate info, equivalent to authentication credentials, cost info, and personally identifiable knowledge (PII), in a safe method. This may be achieved through the use of safe protocols, equivalent to HTTPS, and encrypting logs with keys or different types of encryption.Log knowledge needs to be dealt with like another delicate knowledge in a corporation. Log knowledge have to be protected against unauthorized entry and misuse.
OWASP Webhook Safety Finest Practices: Implementation
Implementing OWASP webhook safety greatest practices is an important step in guaranteeing the safety and integrity of webhooks in your utility. A well-implemented webhook safety framework can defend towards varied assaults, together with knowledge tampering, unauthorized entry, and denial-of-service.
The Step-by-Step Information to Implementing OWASP Webhook Safety Finest Practices
Implementing OWASP webhook safety greatest practices entails a number of steps. First, make sure that your utility makes use of a safe communication protocol, equivalent to HTTPS, to encrypt knowledge in transit. Subsequent, implement authentication and authorization checks to confirm the identification of incoming webhook requests. You also needs to validate and sanitize user-input knowledge to stop SQL injection and cross-site scripting (XSS) assaults.
Authentication and Authorization
Authentication
Implementing Authentication
To implement authentication for webhooks, you need to use varied strategies, equivalent to
- JSON Internet Tokens (JWT): A token-based strategy that encrypts consumer knowledge and sends it to the shopper.
- Fundamental Auth: A easy authentication technique that requires a username and password to be despatched with the request.
- OAuth: An authentication framework that allows safe authorization and authentication.
Every technique has its personal strengths and weaknesses, and the selection of technique is determined by your utility’s particular necessities.
Authorization
Implementing Authorization
As soon as the consumer is authenticated, you should authorize the consumer to carry out particular actions. This may be achieved by assigning roles and permissions to customers. You need to use
- Function-Based mostly Entry Management (RBAC): Assigns roles to customers based mostly on their job features or duties.
- Attribute-Based mostly Entry Management (ABAC): Assigns permissions based mostly on consumer attributes and the requested useful resource.
These strategies present granular management over consumer entry and make sure that customers solely have the required permissions to carry out their duties.
Validation and Sanitization
Knowledge Validation
To stop SQL injection and XSS assaults, it’s best to validate user-input knowledge. This may be achieved utilizing varied strategies, equivalent to
- Enter validation: Checks the format and kind of user-input knowledge.
- Output encoding: Escapes particular characters in user-input knowledge to stop XSS assaults.
All the time validate and sanitize user-input knowledge, whatever the knowledge kind or origin.
Price Limiting and IP Blocking
To stop denial-of-service (DoS) assaults and brute-force assaults, it’s best to implement price limiting and IP blocking mechanisms. These mechanisms can be utilized to
- Prohibit the variety of requests from a single IP tackle inside a timeframe.
- Block IP addresses that exceed the allowed request restrict.
Use APIs like
IP blocking libraries (e.g., IP-Block-IP)
that will help you implement these mechanisms.
Error Dealing with and Logging
To make sure that your webhook safety implementation is strong and dependable, it’s best to implement error dealing with and logging mechanisms. These mechanisms can be utilized to
- Log requests and errors.
- Monitor request charges and IP addresses.
Use APIs like
Error-tracking APIs (e.g., New Relic, Splunk)
that will help you implement these mechanisms.
Testing and Validation
Testing and validating your webhook safety implementation is essential to make sure that it’s working as anticipated. It is best to
- Take a look at for vulnerabilities.
- Carry out penetration testing and vulnerability scanning.
Use instruments like
Auditing instruments (e.g., OWASP ZAP)
that will help you carry out these assessments.
Final Conclusion
In conclusion, OWASP Webhook Safety Finest Practices are important for guaranteeing the safe supply of notifications and knowledge between net functions. By implementing the very best practices Artikeld on this article, you may defend your webhooks from widespread safety dangers and make sure the integrity of your net functions. Bear in mind to at all times prioritize safety in your net improvement tasks, and by no means hesitate to achieve out for assist for those who want it.
Clarifying Questions: Owasp Webhook Safety Finest Practices
What’s OWASP, and why is it vital for webhook safety?
OWASP (Open Internet Utility Safety Challenge) is a non-profit group devoted to enhancing the safety of net functions. OWASP supplies tips, instruments, and assets for builders to implement safe coding practices and stop safety vulnerabilities. Within the context of webhook safety, OWASP’s tips and greatest practices assist make sure the safe supply of notifications and knowledge between net functions.
How can I forestall authentication and authorization points with webhooks?
To stop authentication and authorization points with webhooks, it’s best to implement safe authentication protocols, equivalent to JSON Internet Tokens (JWT), and use role-based entry management (RBAC) to limit entry to approved customers and providers.
What’s knowledge validation, and the way does it relate to webhook safety?
Knowledge validation is the method of guaranteeing that incoming knowledge meets sure standards and is free from malicious code or content material. Within the context of webhook safety, knowledge validation helps forestall webhooks from being exploited by guaranteeing that incoming knowledge is correctly sanitized and validated towards anticipated codecs.