pmbok prince2 threat administration stakeholder communication finest practices units the stage for this enthralling narrative, providing readers a glimpse right into a story that’s wealthy intimately and brimming with originality from the outset.
The PMBOK and Prince2 mission administration frameworks present a construction for managing dangers, and stakeholder communication is essential to make sure that dangers are successfully communicated and managed. Efficient communication helps mitigate the influence of dangers, and it is important for mission administration success.
PMBOK Information to Threat Administration
The Challenge Administration Physique of Information (PMBOK) information gives a complete framework for managing dangers in tasks. Efficient threat administration is essential for guaranteeing the success of tasks and minimizing potential losses.
Position of Threat Administration within the PMBOK Framework
Threat administration performs an important function within the PMBOK framework by figuring out, assessing, and mitigating potential dangers that would influence the mission. It ensures that the mission staff is conscious of potential dangers and has a plan in place to handle them.
Course of Teams and Information Areas Associated to Threat Administration
Threat administration is an integral a part of the mission administration course of, and it includes a number of course of teams and data areas. The next desk illustrates the method teams and data areas associated to threat administration within the PMBOK framework.
The Course of Teams and Information Areas Associated to Threat Administration are as follows:
| Course of Group | Information Space | Description |
| Initiating | Threat Administration | Plan threat administration |
| Planning | Threat Administration | Determine dangers |
| Monitoring & | | |
| Controlling | Threat Administration | Implement threat administration|
Examples of Threat Administration Actions within the PMBOK Framework, Pmbok prince2 threat administration stakeholder communication finest practices
Some examples of threat administration actions within the PMBOK framework embrace:
- Figuring out potential dangers by way of stakeholder engagement, historic knowledge, and skilled judgment.
- Assessing the probability and influence of potential dangers utilizing strategies resembling chance and influence matrices.
- Growing methods to mitigate or keep away from potential dangers, resembling transferring threat to a 3rd occasion or avoiding the chance altogether.
- Establishing a threat administration plan to information the mission staff in addressing potential dangers.
Key Ideas and Strategies
Some key ideas and strategies utilized in threat administration embrace:
- Qualitative threat evaluation: A course of used to establish and prioritize potential dangers primarily based on their probability and influence.
- Quantitative threat evaluation: A course of used to estimate the potential value or influence of a possible threat.
- Threat classes: A framework used to categorise dangers into classes resembling mission, operational, and exterior dangers.
Finest Practices
Some finest practices in threat administration embrace:
- Constantly monitoring and reviewing the chance administration plan to make sure it stays efficient.
- Encouraging a tradition of transparency and open communication amongst stakeholders to facilitate early threat identification and mitigation.
- Utilizing various views and experience to make sure complete threat evaluation.
Stakeholder Communication in Challenge Administration
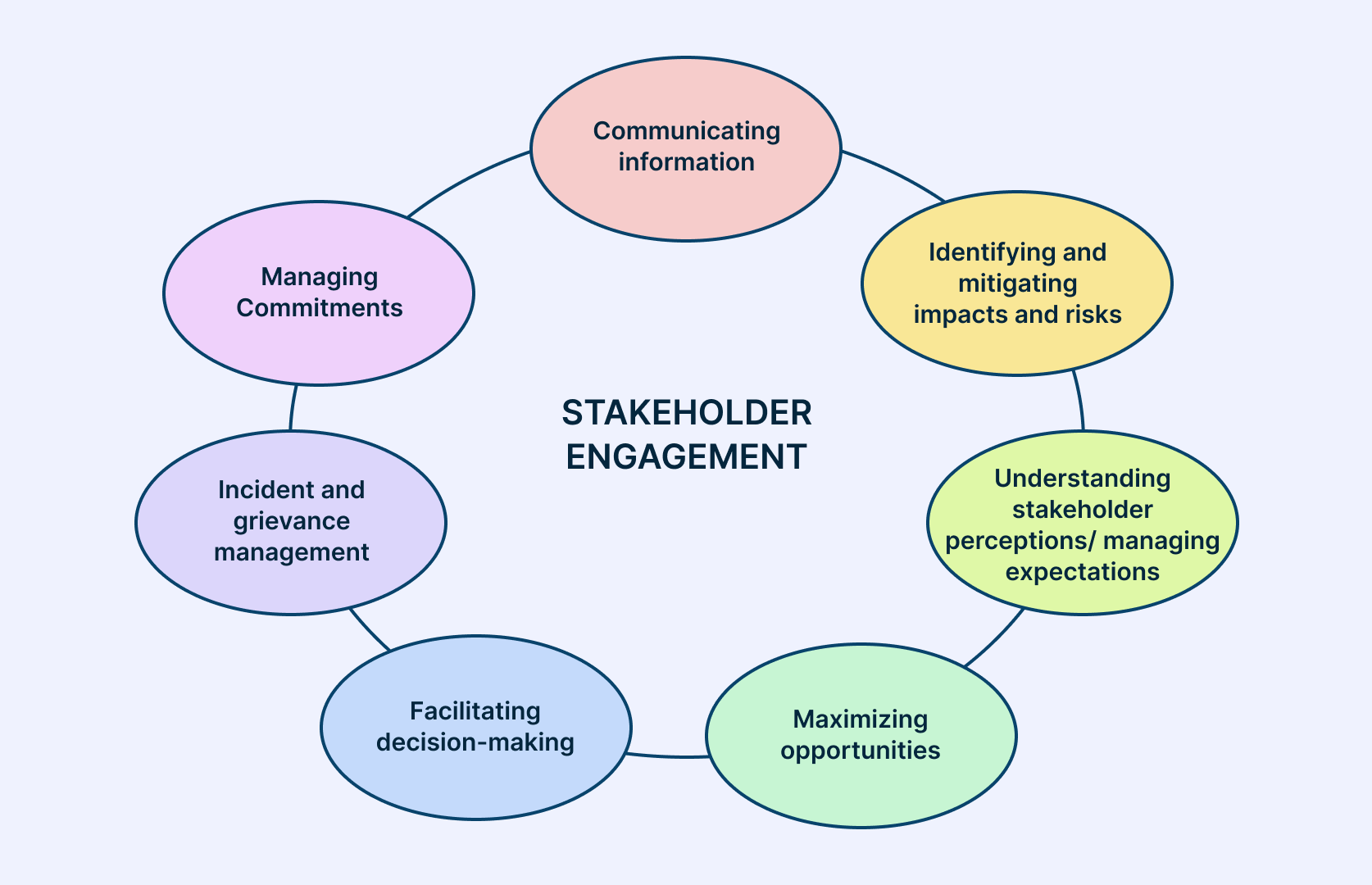
Stakeholder communication is a important element of efficient mission administration. It includes partaking with stakeholders to make sure that their wants and expectations are aligned with mission aims. By successfully speaking with stakeholders, mission managers can mitigate dangers, establish alternatives, and construct belief with stakeholders.
Efficient stakeholder communication requires a deep understanding of the stakeholder panorama, their wants, and their communication preferences.
Varieties of Stakeholders in Challenge Administration
Stakeholders in mission administration will be categorized into a number of sorts primarily based on their stage of curiosity, involvement, and affect. The important thing stakeholders embrace:
– Sponsor: The one who initiates and funds the mission.
– Challenge Supervisor: The particular person liable for planning, executing, and delivering the mission.
– Group Members: The individuals engaged on the mission to attain the aims.
– Prospects/Finish-Customers: The individuals who will use the mission deliverables.
– Suppliers/Distributors: The individuals who present items or companies to the mission.
– Stakeholder Committees: The group of stakeholders who present path and steering on the mission.
– Regulators/Auditors: The individuals who be certain that the mission complies with legal guidelines, laws, and requirements.
Every sort of stakeholder has a novel function and set of expectations within the mission. Understanding these roles and expectations is essential for efficient stakeholder communication.
Prioritizing and Categorizing Stakeholders
Prioritizing and categorizing stakeholders is important for efficient stakeholder communication. This includes assessing the extent of affect, curiosity, and influence that every stakeholder has on the mission.
– Excessive-impact, high-influence stakeholders: These stakeholders have a major influence on the mission and may affect the mission final result.
– Excessive-impact, low-influence stakeholders: These stakeholders have a major influence on the mission however lack the affect to alter the mission final result.
– Low-impact, high-influence stakeholders: These stakeholders have restricted influence on the mission however have vital affect over the mission final result.
– Low-impact, low-influence stakeholders: These stakeholders have restricted influence and affect on the mission.
Prioritizing and categorizing stakeholders helps mission managers to allocate assets successfully and deal with speaking with the stakeholders who’ve the best influence on the mission.
Stakeholder Communication Methods
Efficient stakeholder communication methods contain understanding the stakeholder wants, preferences, and behaviors. Some methods embrace:
– Common Progress Stories: Offering common updates on mission progress, milestones achieved, and challenges confronted.
– Stakeholder Evaluation: Conducting stakeholder evaluation to establish stakeholder wants, expectations, and preferences.
– Communication Channels: Figuring out the best communication channels for every stakeholder, resembling e mail, cellphone, or face-to-face conferences.
– Battle Decision: Establishing a course of for resolving conflicts and addressing stakeholder issues promptly.
– Suggestions Mechanisms: Establishing suggestions mechanisms to make sure stakeholder issues and strategies are heard and addressed.
By implementing these methods, mission managers can be certain that stakeholders are engaged, knowledgeable, and aligned with mission aims.
Participating Stakeholders in Threat Administration
Participating stakeholders in threat administration includes figuring out, assessing, and prioritizing dangers primarily based on stakeholder enter. This includes:
– Conducting stakeholder threat assessments to establish potential dangers and alternatives.
– Prioritizing dangers primarily based on stakeholder enter and mission aims.
– Growing mitigation methods to handle high-priority dangers.
– Constantly monitoring and reviewing dangers to make sure that they’re aligned with stakeholder wants and expectations.
By partaking stakeholders in threat administration, mission managers can be certain that dangers are addressed proactively, and stakeholders are knowledgeable and aligned with mission aims.
Finest Practices in Challenge Threat Administration: Pmbok Prince2 Threat Administration Stakeholder Communication Finest Practices
Challenge threat administration is a vital side of guaranteeing the success of any mission. It includes figuring out, assessing, and mitigating potential dangers that would influence the mission’s aims, timeline, finances, and high quality. Finest practices in mission threat administration are important to reduce the probability and influence of dangers, guarantee mission success, and construct stakeholder belief.
Significance of Integrating Threat Administration into Challenge Planning and Execution
Threat administration needs to be an integral a part of mission planning and execution. This includes incorporating threat administration ideas and practices into every stage of the mission lifecycle. By doing so, mission groups can establish potential dangers early on and develop methods to mitigate or keep away from them.
Efficient integration of threat administration into mission planning and execution requires a risk-aware tradition, clear stakeholder expectations, and a well-defined threat administration course of. This contains figuring out potential dangers, assessing their probability and influence, and growing mitigation plans. By integrating threat administration into mission planning and execution, mission groups can:
– Improve mission success by minimizing the probability and influence of dangers
– Enhance stakeholder satisfaction by demonstrating a proactive method to threat administration
– Scale back mission prices and timelines by figuring out and mitigating potential dangers early on
Benchmarking and Metrics
Efficient mission threat administration requires the usage of benchmarks and metrics to measure and monitor dangers. This includes growing a threat scorecard that tracks the probability and influence of dangers, and monitoring mission efficiency towards established benchmarks. By utilizing benchmarks and metrics, mission groups can:
– Determine areas of excessive threat and develop focused mitigation methods
– Exhibit accountability and transparency in threat administration
– Enhance threat administration by constantly monitoring and evaluating mission efficiency
Widespread Pitfalls in Challenge Threat Administration
Regardless of the significance of mission threat administration, many tasks nonetheless fail to adequately handle dangers. Widespread pitfalls in mission threat administration embrace:
– Not figuring out and assessing potential dangers
– Failing to develop efficient mitigation plans
– Not partaking stakeholders within the threat administration course of
– Not monitoring and reviewing mission dangers often
– Not having a transparent threat administration course of
To keep away from these pitfalls, mission groups ought to:
– Develop a complete threat administration plan
– Have interaction stakeholders within the threat administration course of
– Constantly monitor and evaluation mission dangers
– Develop efficient mitigation plans
– Have a transparent threat administration course of
Advantages of Challenge Threat Administration
Efficient mission threat administration provides quite a few advantages, together with:
– Improved mission success by minimizing the probability and influence of dangers
– Enhanced stakeholder satisfaction by demonstrating a proactive method to threat administration
– Lowered mission prices and timelines by figuring out and mitigating potential dangers early on
– Improved mission repute by demonstrating a dedication to threat administration
By understanding the advantages of mission threat administration, mission groups can prioritize threat administration and make sure the success of their tasks.
Challenge Threat Administration Insurance policies and Procedures
Efficient mission threat administration requires clear insurance policies and procedures to information the chance administration course of. This contains:
– Threat administration plan: Artikels the chance administration method, course of, and procedures
– Threat scorecard: tracks the probability and influence of dangers
– Mitigation plans: Artikels methods to mitigate or keep away from dangers
– Threat monitoring and evaluation course of: ensures common evaluation and evaluation of mission dangers
By establishing clear insurance policies and procedures, mission groups can guarantee constant and efficient threat administration all through the mission lifecycle.
Examples of Challenge Threat Administration Insurance policies and Procedures
Listed below are some examples of mission threat administration insurance policies and procedures:
– Threat administration plan: Artikels the chance administration method, course of, and procedures
– Threat scorecard: tracks the probability and influence of dangers
– Mitigation plans: Artikels methods to mitigate or keep away from dangers
– Threat monitoring and evaluation course of: ensures common evaluation and evaluation of mission dangers
By establishing clear insurance policies and procedures, mission groups can guarantee constant and efficient threat administration all through the mission lifecycle.
Efficient Communication of Challenge Dangers to Stakeholders

Efficient communication of mission dangers to stakeholders is essential for guaranteeing that everybody concerned within the mission is conscious of potential points and is aware of what to do in the event that they come up. This permits stakeholders to make knowledgeable choices, plan for potential dangers, and mitigate their influence. Efficient communication of mission dangers additionally helps to construct belief and confidence amongst stakeholders.
Threat Presentation and Communication
To current mission dangers in a transparent and concise method, mission managers ought to use easy language and keep away from utilizing technical jargon or advanced terminology. Dangers will be introduced utilizing numerous instruments resembling threat matrices, SWOT evaluation, and threat registers. These instruments assist to categorize dangers primarily based on their probability and influence and supply a transparent visible illustration of the dangers.
Threat Presentation needs to be concise and to the purpose, specializing in probably the most important data. It ought to embrace the next:
- Threat description
- Threat proprietor
- Present standing
- Motion plan
- Determination required
Participating Stakeholders in Threat Administration
Participating stakeholders in threat administration actions is important for guaranteeing that everybody is conscious of potential dangers and is concerned in figuring out and mitigating them. Stakeholders will be engaged by way of common threat evaluation conferences, the place they supply enter on threat evaluation and mitigation methods. They can be concerned within the improvement of threat administration plans and in monitoring progress towards threat mitigation actions.
Along with common conferences, stakeholders will be engaged by way of numerous communication channels, together with e mail updates, mission administration software program, and dashboards. This ensures that stakeholders have entry to real-time data on mission dangers and may increase issues or present enter as wanted.
Varieties of Threat-Associated Data to Talk to Stakeholders
Challenge managers ought to talk risk-related data to stakeholders in a well timed and clear method. This could embrace:
- Threat identification and evaluation outcomes
- Threat mitigation plans and methods
- Progress towards threat mitigation actions
- New dangers or modifications to current dangers
Prioritizing and Focusing Communication on Excessive-Affect Dangers
Challenge managers ought to prioritize communication of high-impact dangers, which have a major influence on the mission schedule, finances, or scope. Excessive-impact dangers needs to be communicated to stakeholders as quickly as they’re recognized, and stakeholders needs to be saved knowledgeable of modifications to those dangers.
When prioritizing communication of high-impact dangers, mission managers ought to contemplate the next elements:
- Affect on mission schedule
- Affect on mission finances
- Affect on mission scope
- Threat probability
- Threat sensitivity
Shows and Stories for Stakeholders
Challenge managers ought to present common displays and studies to stakeholders on mission dangers, together with:
- Threat updates
- Threat evaluation outcomes
- Threat mitigation plans
- Progress towards threat mitigation actions
These displays and studies needs to be concise, clear, and visually interesting, utilizing charts, graphs, and different visible aids to assist stakeholders perceive advanced data.
Clear and concise communication of mission dangers is important for guaranteeing that stakeholders are conscious of potential points and are capable of make knowledgeable choices.
Designing and Implementing Challenge Threat Administration Methods
On this planet of mission administration, navigating uncertainty is a vital process. With numerous variables at play, potential dangers can come up unexpectedly, placing the complete mission in jeopardy. It’s important to design and implement efficient threat administration methods to mitigate these dangers, guarantee mission success, and safeguard the group’s repute. On this part, we are going to delve into the significance of designing and implementing mission threat administration methods, establish and assess potential dangers, and develop and implement mitigation and contingency plans.
Significance of Designing and Implementing Threat Administration Methods
Threat administration methods are very important to mission success as they permit mission managers to proactively establish, assess, and mitigate potential dangers. Efficient threat administration methods assist stop or decrease the influence of dangers, guaranteeing mission deliverables are met on time, inside finances, and to the required high quality requirements. Furthermore, threat administration methods allow mission managers to allocate assets extra effectively, prioritize duties, and be certain that the mission is aligned with organizational objectives.
Key Elements of Profitable Threat Administration Methods
To develop efficient threat administration methods, mission managers should comply with a structured method. The important thing parts of a profitable threat administration technique contain:
-
Threat Identification
Threat identification is step one within the threat administration course of. It includes figuring out potential dangers that would influence the mission. This may be achieved by way of numerous strategies resembling brainstorming, checklists, and skilled judgment. It’s important to contain all stakeholders within the threat identification course of to make sure that all potential dangers are thought of.
- Potential sources of threat embrace modifications in mission scope, schedule, or finances, in addition to exterior elements resembling market fluctuations or regulatory modifications.
- Threat identification needs to be ongoing all through the mission life cycle, with common opinions and updates to make sure that new dangers are recognized and current dangers are reassessed.
- Threat identification needs to be documented and communicated to all stakeholders, together with staff members, sponsors, and stakeholders.
-
Threat Evaluation
Threat evaluation is the method of evaluating the probability and influence of potential dangers. This includes assigning a threat rating to every recognized threat primarily based on its probability and influence. The chance rating is then used to prioritize dangers and develop mitigation and contingency plans.
- The chance rating will be calculated utilizing numerous strategies such because the probability-impact matrix or the anticipated financial worth (EMV) technique.
- Threat evaluation needs to be carried out for all recognized dangers, and the outcomes needs to be documented and communicated to all stakeholders.
- Threat evaluation needs to be ongoing all through the mission life cycle, with common opinions and updates to make sure that new dangers are assessed and current dangers are reassessed.
-
Threat Mitigation
Threat mitigation is the method of growing and implementing plans to cut back or get rid of potential dangers. This may embrace methods resembling threat avoidance, threat switch, or threat discount.
- Threat mitigation plans needs to be developed for all recognized dangers, and the plans needs to be documented and communicated to all stakeholders.
- Threat mitigation plans needs to be often reviewed and up to date to make sure that they continue to be efficient and related.
- Threat mitigation plans needs to be carried out in a well timed method to reduce the influence of dangers.
Growing and Implementing Mitigation and Contingency Plans
Growing and implementing mitigation and contingency plans is a vital step in threat administration. Mitigation plans intention to cut back or get rid of the probability or influence of potential dangers, whereas contingency plans intention to mitigate the influence of dangers which have been realized. The event and implementation of mitigation and contingency plans needs to be primarily based on the chance evaluation and mitigation methods Artikeld within the threat administration plan.
“A well-designed threat mitigation plan might help stop or decrease the influence of dangers, guaranteeing mission success and safeguarding the group’s repute.”
In conclusion, designing and implementing efficient threat administration methods is important to mission success. By figuring out, assessing, and mitigating potential dangers, mission managers can be certain that their tasks are delivered on time, inside finances, and to the required high quality requirements.
Concluding Remarks
_Configuration_Management_Strategy.jpg)
This complete Artikel gives an entire view of find out how to handle dangers utilizing the PMBOK and Prince2 frameworks and the way stakeholder communication is essential for mission success.
Making use of these finest practices will make it easier to develop efficient threat administration methods and guarantee profitable mission outcomes.
Person Queries
Q: What’s the major function of threat administration within the PMBOK framework?
A: The first function of threat administration within the PMBOK framework is to establish, analyze, prioritize, and reply to dangers that would have an effect on the mission.
Q: How does the Prince2 threat administration methodology differ from the PMBOK method?
A: The Prince2 threat administration methodology is a cyclical course of that includes figuring out, assessing, and prioritizing dangers, whereas the PMBOK method is a extra linear course of that includes planning, figuring out, assessing, and responding to dangers.
Q: What’s the significance of stakeholder communication in efficient mission administration?
A: Stakeholder communication is important for efficient mission administration because it helps be certain that stakeholders are knowledgeable and engaged all through the mission lifecycle.