Which greatest describes the terrorist planning cycle – Delving into understanding terrorist planning cycle, this introduction immerses readers in a novel and compelling narrative that highlights the significance of recognizing key parts and levels concerned in terroristic actions.
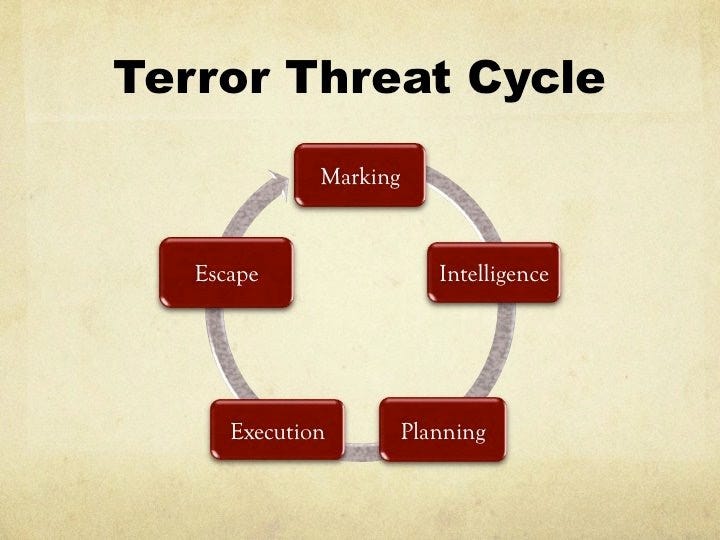
The terrorist planning cycle is a fancy course of that entails varied levels, ranging from reconnaissance and ending with operational execution. Every stage is essential in making certain the success of a terrorist assault. This text will present an in-depth look into the completely different levels of the terrorist planning cycle.
Understanding the Idea of Terrorist Planning Cycle
The terrorist planning cycle refers back to the sequence of levels concerned in planning and executing a terrorist assault. This cycle is important in understanding the conduct and techniques of terrorist organizations, because it supplies worthwhile insights into their motivations, capabilities, and vulnerabilities. The planning cycle is a fancy and dynamic course of that entails a number of levels, every with its personal distinctive challenges and alternatives for disruption or foiling.
Key Components Concerned within the Terrorist Planning Cycle, Which greatest describes the terrorist planning cycle
The terrorist planning cycle usually entails the next key parts:
- Recruitment and radicalization: This stage entails figuring out and recruiting people who’re sympathetic to the trigger and keen to bear radicalization. Radicalization is the method of persuading people to undertake extremist ideologies and interact in violent conduct.
- Planning and analysis: Terrorists conduct in depth analysis and planning to establish vulnerabilities within the goal, select the simplest techniques, and purchase needed sources and supplies.
- Coaching and preparation: Terrorists obtain coaching and put together for the assault, which can embrace buying abilities reminiscent of firearms dealing with, explosives use, and tactical operations.
- Execution and contingency planning: Terrorists execute the assault, whereas additionally having contingency plans in place to deal with sudden occasions or adjustments in circumstances.
- Escape and evasion: Terrorists try to flee and evade legislation enforcement and intelligence businesses, which can contain utilizing protected homes, hiding in crowded areas, and using false identities.
Distinction between Planning and Operational Levels
The planning and operational levels are distinct phases throughout the terrorist planning cycle. The starting stage entails gathering intelligence, choosing targets, and growing methods, whereas the operational stage entails executing the assault and responding to contingencies. Understanding these two levels is important in disrupting or foiling terrorist plans.
Advanced Terrorist Plots and Their Planning Phases
A number of notable terrorist plots have demonstrated the complexity and multifaceted nature of the planning cycle.
– The 9/11 assaults concerned a complete starting stage, which included surveillance, communication, and logistical preparations, in addition to an in depth operational plan.
– The 2008 Mumbai terrorist assault concerned a number of teams planning and coordinating to execute a fancy assault on varied targets.
– The 2013 Boston Marathon bombing was a results of in depth on-line analysis, procurement of supplies, and tactical planning by the perpetrators.
Cases The place the Planning Cycle Was Disrupted or Foiled
A number of cases reveal the effectiveness of legislation enforcement and intelligence businesses in disrupting or foiling terrorist plans.
– The disruption of a deliberate assault on the New York Metropolis subway system in 1994 serves for instance of efficient counter-terrorism efforts.
– The 2001 shoe bomber plot was foiled on the final second, highlighting the significance of vigilant journey screening and intelligence gathering.
– The 2014 New York Metropolis Occasions Sq. bombing try was thwarted by efficient intelligence gathering and legislation enforcement operations.
Understanding the terrorist planning cycle is important in growing efficient counter-terrorism methods. Figuring out vulnerabilities and disrupting the planning course of can forestall terrorist assaults from occurring within the first place.
Levels of the Terrorist Planning Cycle
The terrorist planning cycle is a scientific strategy utilized by terrorist organizations to realize their aims. It entails a number of levels that contribute to the ultimate purpose of finishing up a terrorist assault. Understanding these levels is essential for legislation enforcement businesses, policymakers, and most of the people to forestall and counter terrorist threats.
The planning cycle usually consists of a number of levels, every of which is important to the success of the operation. These levels are:
Stage 1: Planning and Goal Choice
On this stage, terrorist organizations establish potential targets and develop a plan to assault them. They assess the vulnerability of the goal, the extent of safety, and the potential impression of the assault. The planning staff considers varied elements, together with the goal’s accessibility, the presence of safety forces, and the potential for casualties.
- The planning staff identifies potential targets, reminiscent of authorities buildings, public transportation programs, or crowded areas.
- They assess the goal’s vulnerability and develop a plan to assault it, considering elements reminiscent of safety measures, surveillance, and intelligence gathering.
- The staff considers the potential penalties of the assault, together with the variety of casualties and the impression on the group.
Stage 2: Reconnaissance and Surveillance
On this stage, terrorist organizations collect details about the goal and its environment. They conduct reconnaissance to establish vulnerabilities, assess safety measures, and collect intelligence on potential witnesses or investigators. Surveillance is used to observe the goal’s actions and establish patterns of conduct.
- Terrorist organizations use varied strategies to collect data, together with espionage, hacking, and social engineering.
- They conduct surveillance to establish potential targets, assess safety measures, and collect intelligence on potential witnesses or investigators.
- Surveillance is used to observe the goal’s actions and establish patterns of conduct, reminiscent of schedules and routine actions.
Stage 3: Useful resource Mobilization
On this stage, terrorist organizations collect the sources wanted to hold out the assault. They purchase funding, tools, and personnel to help the operation. They might additionally set up a logistics community to produce the operation with supplies and personnel.
- Terrorist organizations purchase funding by means of varied means, together with donations, extortion, and theft.
- They collect tools and personnel wanted to hold out the assault, reminiscent of weapons, explosives, and autos.
- They set up a logistics community to produce the operation with supplies and personnel, together with communication tools and medical provides.
Stage 4: Operations
On this stage, terrorist organizations perform the assault. They use the sources gathered within the earlier levels to execute the plan and obtain their aims. The operation might contain a sequence of actions, together with infiltration, sabotage, and assassination.
- Terrorist organizations use varied techniques to hold out the assault, together with bombings, shootings, and stabbings.
- They might use superior know-how, reminiscent of drones or hacking instruments, to boost the effectiveness of the operation.
- The operation is commonly carried out in a coordinated method, with a number of groups working collectively to realize the target.
Stage 5: Escape and Evasion
On this stage, terrorist organizations try to flee and evade seize after the assault. They use varied techniques, together with fleeing the scene, concealing proof, and disguising themselves. They might additionally set up a protected home or hideout to evade pursuit.
- Terrorist organizations use varied techniques to flee and evade seize, together with fleeing the scene, concealing proof, and disguising themselves.
- They might set up a protected home or hideout to evade pursuit, the place they’ll relaxation, get better, and plan their subsequent transfer.
- They might additionally use communication tools and encryption to remain in contact with supporters and coordinate their escape.
Stage 6: Exploitation and Manipulation
On this stage, terrorist organizations try to use the aftermath of the assault to realize their aims. They use varied techniques, together with propaganda, manipulation of the media, and exploitation of the victims’ households.
- Terrorist organizations use propaganda and manipulation of the media to realize their aims and affect public opinion.
- They might exploit the victims’ households to additional their agenda, utilizing their struggling to realize sympathy and help.
- They might additionally use the assault to recruit new members and lift funds, exploiting the outrage and indignation of the group.
Stage 7: Consolidation and Planning
On this stage, terrorist organizations consolidate their good points and plan their subsequent transfer. They assess the impression of the assault, consider their strengths and weaknesses, and plan their subsequent operation.
- Terrorist organizations assess the impression of the assault, evaluating their strengths and weaknesses and figuring out areas for enchancment.
- They plan their subsequent operation, utilizing the teachings realized from the earlier assault to refine their technique and techniques.
- They might additionally set up new cells or sleeper brokers, making ready for the following assault by establishing a community of supporters and operatives.
Goal Choice and Planning
Goal choice is a vital step within the terrorist planning cycle, the place terrorists establish and select their goal to realize their objectives. This course of is influenced by varied elements, together with the goal’s symbolic worth, potential impression, accessibility, and vulnerability. The collection of a goal can considerably impression the success of a terrorist assault, because it determines the extent of injury, casualties, and disruption triggered.
The method of goal evaluation entails evaluating the potential penalties of hanging a selected goal. This entails assessing the potential impression on the goal’s inhabitants, the encircling space, and the broader group. Terrorists may additionally take into account the goal’s symbolic worth, reminiscent of its cultural or historic significance, in addition to its potential to generate media consideration and worldwide condemnation.
Elements Influencing Goal Choice
Terrorists take into account a number of elements when choosing a goal, together with:
- Symbolic worth: Targets with excessive symbolic worth, reminiscent of authorities buildings, iconic landmarks, or locations of worship, are sometimes chosen for his or her potential to generate important media consideration and worldwide condemnation.
- Potential impression: Targets with excessive potential impression, reminiscent of transportation hubs, buying facilities, or crowded public areas, are sometimes chosen for his or her skill to trigger important injury and casualties.
- Accessibility: Targets which are simply accessible, reminiscent of these with minimal safety measures or insufficient surveillance, are sometimes chosen for his or her ease of assault.
- Vulnerability: Targets which are perceived as weak, reminiscent of these with insufficient safety measures or poor emergency response protocols, are sometimes chosen for his or her potential to be simply exploited.
Examples of Profitable and Failed Terrorist Assaults
Profitable terrorist assaults typically reveal a radical understanding of the goal’s vulnerabilities and the flexibility to use them successfully. For instance:
- The 9/11 assaults on the World Commerce Heart in New York Metropolis, which highlighted the vulnerability of tall buildings to hijacked plane.
- The 2005 London bombings, which focused town’s transportation community and highlighted the vulnerability of public areas to assaults.
Failed terrorist assaults typically consequence from miscalculations or misjudgments in regards to the goal’s vulnerabilities. For instance:
- The 2001 shoe bomber plot, which was meant to focus on an airplane however was foiled by a mix of safety measures and good luck.
- The 2015 Charlie Hebdo assault in Paris, which focused a satirical journal however was foiled by the journal’s safety measures and the bravery of its workers.
Vulnerabilities of Completely different Varieties of Targets
| Goal | Vulnerability | Mitigation |
| Authorities buildings | Weak safety measures, insufficient surveillance | Enhance safety measures, improve surveillance |
| Transportation hubs | Excessive foot visitors, minimal safety measures | Improve safety measures, enhance surveillance |
| Procuring facilities | Excessive foot visitors, insufficient safety measures | Improve safety measures, enhance emergency response protocols |
| Locations of worship | Symbolic worth, insufficient safety measures | Enhance safety measures, improve surveillance |
| Public areas | Excessive foot visitors, insufficient safety measures | Improve safety measures, enhance emergency response protocols |
Logistic help and useful resource acquisition are essential parts of the terrorist planning cycle. Terrorists want to amass varied sources, together with financing, personnel, tools, and protected havens, to plan and execute their operations. These sources allow terrorists to maintain their actions, reply to operational disruptions, and adapt to altering circumstances.
Financing and Fund-Elevating
Financing is a important side of terrorist planning. Terrorists use varied strategies to boost funds, together with donations, extortion, kidnapping for ransom, and theft. In addition they exploit authentic monetary channels, reminiscent of cash laundering and cash-based transactions. The proceeds from these actions are then funneled into the terrorist group’s operational funds.
The monetary help allows terrorists to amass the required sources, together with tools, transportation, and protected homes. It additionally permits them to pay their operatives, fund journey, and set up operational networks.
- Terrorists typically use shell corporations, charities, and different entrance organizations to launder funds and conceal their monetary actions.
- In addition they exploit the weaknesses within the international monetary system, reminiscent of the shortage of efficient anti-money laundering controls and the convenience of transferring money throughout borders.
- Some terrorist organizations, reminiscent of Al-Qaeda, have established advanced financing networks that contain a number of nations and operatives.
- Others, just like the Islamic State, have relied on oil gross sales and different illicit sources of revenue to fund their operations.
Useful resource Acquisition
Terrorists purchase sources by means of varied means, together with:
- Stealing or hijacking autos, tools, and different supplies.
- Buying items and companies from native markets or on-line platforms.
- Borrowing or renting tools and amenities from sympathizers or unsuspecting people.
- Buying sources from different extremist teams or organizations.
The acquisition of sources is important to a terrorist group’s operational capabilities. It allows them to plan and execute assaults, transport personnel and tools, and preserve protected havens.
| Useful resource | Methodology | Group |
|---|---|---|
| Funding | Donations and extortion | Al-Qaeda |
| Transportation | Hijacking and buying | The Islamic State |
| Gear | Stealing and borrowing | Boko Haram |
| Affiliation | Establishing relationships with allies | Hezbollah |
Examples of Profitable Logistic Operations
A number of terrorist organizations have efficiently executed logistic operations that supported their assaults. For instance:
- Al-Qaeda used a fancy community of protected homes, resorts, and different amenities to plan and execute the 9/11 assaults.
- The Islamic State established a classy provide chain that enabled them to import oil, tools, and personnel from throughout the globe.
- Boko Haram used stolen autos and tools to hold out assaults in Nigeria and different elements of West Africa.
These examples illustrate the significance of logistic help and useful resource acquisition in terrorist planning. Efficient logistical capabilities allow terrorist organizations to plan and execute advanced assaults, maintain their operations over time, and adapt to altering circumstances.
Operational Planning and Execution: Which Finest Describes The Terrorist Planning Cycle
Operational planning and execution is the ultimate stage of the terrorist planning cycle, the place the terrorist group implements their fastidiously laid plans. This stage is essential, because it determines the success or failure of the assault. On this stage, the main focus is on making certain that the operation is executed easily, with none main problems or setbacks.
Key Elements of Operational Planning
Operational planning entails a spread of key parts, together with timing and coordination. The terrorists should make sure that all of the logistical particulars, such because the motion of personnel, tools, and provides, are in place. They have to additionally coordinate with different actors, reminiscent of sympathizers or co-conspirators, to make sure a seamless execution of the plan. The timing of the assault can also be essential, because it should coincide with the optimum second to trigger most injury and disruption.
Methods Employed by Terrorists to Execute Assaults
Terrorist organizations make use of a spread of strategies to execute assaults, together with using intelligence gathering, surveillance, and reconnaissance. They might additionally use false identities, disguises, and different types of deception to mix in with their environment and keep away from detection. As well as, they might use superior know-how, reminiscent of drones and social media, to collect data, coordinate assaults, and disseminate propaganda. Moreover, they might use techniques reminiscent of ambushes, booby traps, and bombings to inflict most injury.
Examples of Profitable and Failed Assaults
There have been quite a few profitable and failed assaults by terrorist organizations through the years. For instance, the 9/11 assaults in the US in 2001 had been a masterclass in operational planning and execution, with the terrorists utilizing a mix of intelligence gathering, surveillance, and deception to hold out a devastating assault that resulted within the lack of hundreds of lives. In distinction, the 2013 Boston Marathon bombing, additionally carried out by terrorists, was a failed assault that resulted within the lack of lives however failed to realize its meant goal of inflicting widespread chaos and destruction. The Paris assaults in 2015, carried out by terrorists affiliated with ISIS, had been a profitable assault that resulted within the lack of dozens of lives and triggered widespread disruption to town.
The Significance of Adaptability and Contingency Planning
Operational planning and execution requires adaptability and contingency planning to make sure that the operation is executed easily, even within the face of sudden challenges or setbacks. Terrorist organizations should be capable to adapt to altering circumstances, such because the presence of safety forces, and have contingency plans in place to take care of sudden occasions. They have to additionally be capable to talk successfully with their operatives and sympathizers to make sure that everyone seems to be on the identical web page and that the operation is executed as deliberate.
Examples of Terrorist Adaptability and Contingency Planning
Terrorist organizations have demonstrated their skill to adapt and plan for contingencies in quite a few methods. For instance, using cellphone know-how has enabled terrorist operatives to speak with one another and obtain updates on the operation in real-time. As well as, using safe on-line platforms has enabled terrorist organizations to coordinate their actions and disseminate propaganda with out being detected by safety forces. Moreover, using social media and on-line fundraising platforms has enabled terrorist organizations to boost funds and recruit sympathizers from around the globe.
Challenges in Operational Planning and Execution
Operational planning and execution is a fancy and difficult course of, fraught with dangers and uncertainties. Terrorist organizations should navigate a spread of challenges, together with the presence of safety forces, the necessity to keep away from detection, and the necessity to execute the operation easily. They have to additionally be capable to adapt to altering circumstances and have contingency plans in place to take care of sudden occasions. As well as, they need to be capable to talk successfully with their operatives and sympathizers to make sure that everyone seems to be on the identical web page and that the operation is executed as deliberate.
Communication and Coordination
Terrorist teams make use of subtle communication methods to facilitate coordination and planning in the course of the terrorist planning cycle. This stage is important, because it allows the group to disseminate data, allocate duties, and synchronize efforts with out compromising operational safety.
Safe Communication Channels
Terrorists depend on safe communication channels to make sure operational safety. These channels embrace encrypted messaging apps, safe e mail companies, and encrypted communication protocols. Through the use of these channels, terrorists can shield their communications from interception and monitoring by legislation enforcement businesses.
Strategies Utilized by Terrorists for Communication and Coordination
Terrorist teams make use of a spread of strategies for communication and coordination. These embrace:
- Closed social media teams and chat rooms
- Finish-to-end encrypted messaging apps
- Safe e mail companies and protocols
- Code phrases and ciphers
- In-person conferences and clandestine gatherings
These strategies allow terrorists to speak with one another discreetly and securely, making certain that their plans and operations stay undetected by legislation enforcement businesses.
Examples of Profitable and Failed Communication Channels
Terrorist teams have efficiently used varied communication channels for coordination and planning. For instance:
- The Islamic State (ISIS) has used encrypted messaging apps, reminiscent of Telegram and WhatsApp, to speak with its members and coordinate operations.
- Al-Qaeda has employed safe e mail companies and protocols to speak with its associates and plan operations.
- Nonetheless, some terrorist teams have additionally skilled failures of their communication channels. For example, the 2009 underwear bomber, Umar Farouk Abdulmutallab, was found by intelligence businesses resulting from a communication error involving a cryptic message on a web based discussion board.
Strengths and Weaknesses of Communication Strategies
The next desk highlights the strengths and weaknesses of various communication strategies utilized by terrorists:
| Methodology | Safety | Ease of Use |
|---|---|---|
| Closed social media teams and chat rooms | Average | Excessive |
| Finish-to-end encrypted messaging apps | Excessive | Excessive |
| Safe e mail companies and protocols | Excessive | Low |
| Code phrases and ciphers | Excessive | Low |
| In-person conferences and clandestine gatherings | Low | Low |
This desk illustrates the trade-offs between safety and ease of use for various communication strategies. Whereas some strategies provide excessive safety however low ease of use, others present average safety however excessive ease of use. Terrorist teams should fastidiously weigh these elements when choosing a communication methodology to make sure operational safety.
Contingency Planning and Disaster Administration
Contingency planning and disaster administration are important parts of terrorist operations, enabling planners to anticipate and reply successfully to sudden conditions or disruptions. By figuring out potential dangers and growing methods to mitigate them, terrorist organizations can decrease the impression of sudden occasions and preserve their operations.
The Significance of Contingency Planning
Contingency planning is crucial for terrorist operations because it permits planners to anticipate and reply to sudden occasions, reminiscent of legislation enforcement interventions, technological failures, or adjustments within the operational atmosphere. This allows them to keep up their aims and decrease the danger of failure or detection. Efficient contingency planning entails figuring out potential dangers, assessing their chance and impression, and growing methods to mitigate or reply to them.
Managing Eventualities in Terrorist Operations
Throughout a terrorist operation, varied situations might come up, and planners have to be ready to deal with them. This contains responding to legislation enforcement interventions, managing the aftermath of a failed operation, and coping with sudden adjustments within the operational atmosphere. A well-planned contingency technique might help terrorist organizations keep forward of those situations and preserve their aims.
Examples of Profitable Contingency Planning
A number of examples illustrate the significance of contingency planning in terrorist operations. One notable instance is the 9/11 assaults, the place Al-Qaeda’s skill to adapt to altering circumstances and reply to sudden occasions allowed them to keep up their aims regardless of the shock assault on the World Commerce Heart. One other instance is the 2002 Bali bombings, the place Jemaah Islamiyah’s contingency planning allowed them to reply successfully to the aftermath of the assault and preserve their operations.
Varieties of Contingency Plans
The next desk Artikels the several types of contingency plans that could be employed in terrorist operations:
| Situation | Response Plan | Mitigation Ways |
| — | — | — |
| Regulation Enforcement Intervention | Evacuate personnel, safe property, and preserve communication | Use encrypted communication channels, implement safe protocols, and designate protected zones |
| Technological Failure | Diversify communication channels, use redundant programs, and implement backup protocols | Often replace and check programs, implement fail-safe options, and designate contingency plans for system failures |
| Change in Operational Atmosphere | Adapt plans, alter timelines, and reassess aims | Keep knowledgeable about altering circumstances, alter plans accordingly, and preserve flexibility in operations |
| Aftermath of a Failed Operation | Safe proof, preserve operational safety, and coordinate a response | Implement safe protocols, designate a communication channel, and coordinate with different organizations |
| Sudden Occasion | Determine dangers, assess impression, and develop a response plan | Monitor the scenario, assess the danger, and develop a contingency plan to mitigate or reply to the occasion |
Conclusion
Contingency planning and disaster administration are important parts of terrorist operations, enabling planners to anticipate and reply successfully to sudden conditions or disruptions. By figuring out potential dangers and growing methods to mitigate them, terrorist organizations can decrease the impression of sudden occasions and preserve their aims.
Closing Conclusion
In conclusion, understanding the terrorist planning cycle is essential in stopping and countering terroristic actions. By figuring out the important thing parts and levels concerned on this cycle, we will higher put together ourselves to disrupt and defeat terrorist organizations.
Question Decision
What are the important thing parts concerned within the terrorist planning cycle?
The important thing parts concerned within the terrorist planning cycle embrace reconnaissance, goal choice and planning, logistic help and useful resource acquisition, operational planning and execution, communication and coordination, and contingency planning and disaster administration.
How do terrorists purchase sources and logistical help?
Terrorists purchase sources and logistical help by means of varied strategies, together with financing and fund-raising, donations, and theft. In addition they use the web and different communication channels to boost funds and collect help.
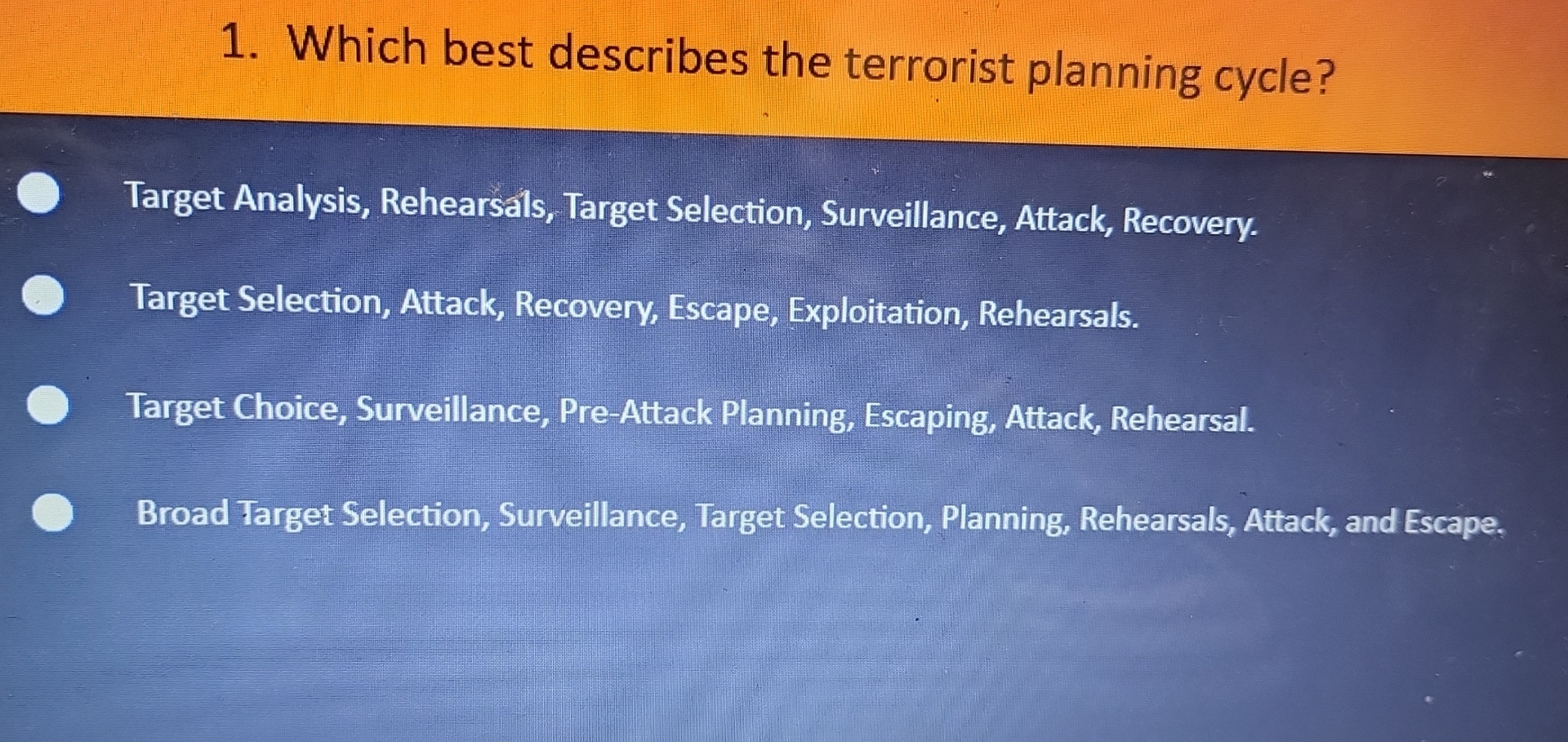
What are the completely different levels of the terrorist planning cycle?
The completely different levels of the terrorist planning cycle embrace reconnaissance, goal choice and planning, logistic help and useful resource acquisition, operational planning and execution, communication and coordination, and contingency planning and disaster administration.